
Law enforcement authorities across the globe disrupted many long-running botnets powered by a malware family dubbed as Gamarue, mostly detected by ESET as Win32/TrojanDownloader.Wauchos and also known as Andromeda, capping a year-plus concerted effort that relied on technical intelligence from Microsoft and ESET researchers.
ESET, having been approached by Microsoft to join the disruption effort, provided a technical analysis for the operation that ultimately knocked Wauchos for the count. ESET researchers closely tracked the botnets, identified their C&C servers for takedown, and kept tabs on what those spreading the threat were installing on victims’ systems. Microsoft then contacted law enforcement with information that included: 464 distinct botnets, 80 associated malware families, and 1,214 domains and IP addresses of the botnet’s C&C servers.
Wauchos: a global scourge
Wauchos has been making the rounds since at least September 2011, having come in five major versions over the years. It has been primarily up for grabs in the dark corners of the internet as a crime kit, enabling anybody with ill intentions to buy a ‘piece’.
The prevalence map based on ESET’s telemetry (Figure 1) shows the global reach of Wauchos, which has created scores of standalone botnets in various parts of the world.

According to Microsoft, the infestation was detected or blocked on an average of nearly 1.1 million machines every month over the past six months.
Throughout its monitoring of the threat, ESET found dozens of C&C servers every month. The bulk of ESET’s research was conducted late last year, with the peak of Wauchos’s activity going back approximately to that time.
“Wauchos is mostly used to steal credentials, and to download and install additional malware onto a system. Thus, if a system is compromised with Wauchos, it’s likely that there will be several other malware families lurking on the same system,” according to ESET researcher Jean-Ian Boutin.
The secondary malware that compromises victim machines after they’re roped into the botnet includes mainly Kasidet, which is also known as Neutrino bot, and is used to conduct distributed denial-of-service (DDoS) attacks, and the Kelihos and Lethic spambots, which have been involved in massive junk mail campaigns.
Due to its modularity, the Wauchos functionalities can easily be expanded by plugins. They include a keylogger and a form grabber, both of which can snatch a user’s personal data, plus a rootkit, which can be used to hide malware’s presence and ultimately ensure its persistence on a compromised system.
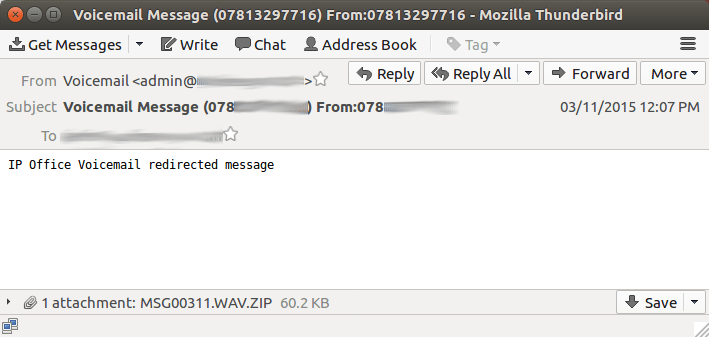
As Wauchos is bought and unleashed by a variety of cybercriminals, the attack vectors used to spread the threat vary just as much. The malware has most commonly been propagated through social media, instant messaging, removable drives, spam (see Figure 2), and exploit kits.
As has been the case with other malware, many Wauchos samples analyzed by ESET were configured to check the system’s keyboard layout. If set to one of Russian, Ukrainian, Belarussian or Kazakh, the code exits without doing anything malicious. This tactic is presumably intended to ensure that the bad actors avoid prosecution in those countries.
Over the years, intelligence provided by ESET has been instrumental in dismantling a number of criminal operations, including the Dorkbot and Mumblehard botnets, and the Avalanche fast-flux network that was employed by many other botnets.
If you are worried that your Windows system might be compromised by Wauchos and are not an ESET customer, you can download and use ESET’s Free Online Scanner, which will remove any threats, including Wauchos, it might find on your system.
A detailed analysis of how ESET helped to disrupt these troublesome botnets is available here: ESET takes part in global operation to disrupt Gamarue.
written by Tomas Foltyn, ESET We Live Security
