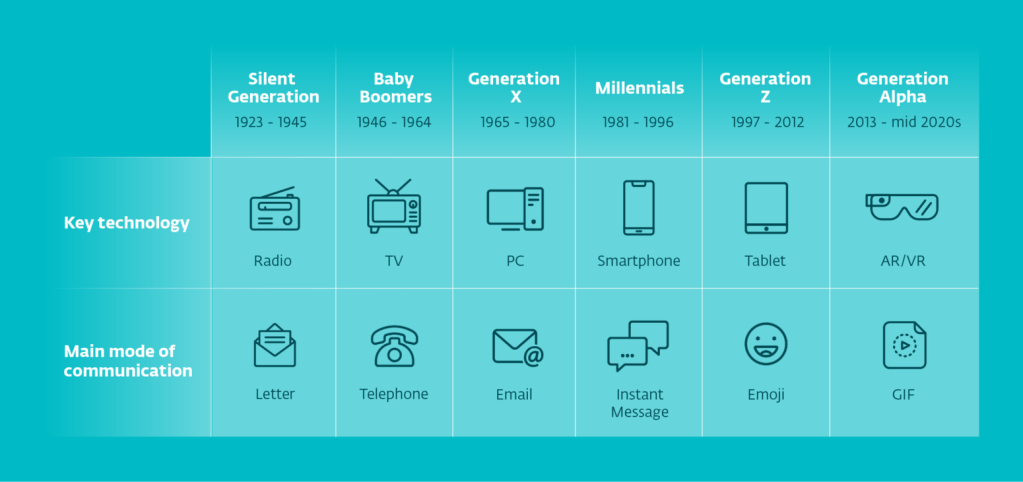
The notion that only young people use the internet is long gone. The fact is that the online world has consumed all of us. We may not like it, but by all of us, we mean toddlers to seniors. And therefore, we should all consider ourselves the “digital generation.” But that does not mean we all perceive and use technology the same way. There are certainly tangible differences in how we interact with technology.
The younger a generation is, the sooner they were likely to have been introduced to technology. On the other hand, older generations may have become familiar to technology later in life, but combined with their life experiences, they might have approached their technology use more responsibly. The approaches different generations take is certainly different; some are earlier adopters of innovations, but one does not lag behind the other.
The Pew Research Center conducted research in 2021, where they measured generations’ use of the digital world. For example, 99% of Gen Z and Millennials claim they use the internet. Gen X has a slightly lower usage, which still comes to 96%, compared to the Baby Boomers, where only 75% claim they use the internet. The interesting finding of the study is that since the year 2000, the gap between the oldest and the youngest internet users has gotten smaller, from 56 to 44 percentage points.
The data doesn’t lie, and proves that in fact all generations are part of the digital world. The difference is their involvement, perception and use. Generations look at technology and innovation based on their own background and knowledge. And that differs among virtually all of them. Many of them came into a world that was already full of technology, and others had to adapt to it at a more mature age.
And the same goes for digital security. Contrary to popular belief, growing up with technology does not automatically make you more conscious of digital privacy and security. Industry leader NTT’s study shows that people over 30 are more likely to adopt better security practices than the younger generation, Generation Z. Gen Z, even though they grew up surrounded by technology and the risks it poses, are much more laid back and less responsible. They value flexibility and productivity over caution and responsibility. Furthermore, the study found that almost 40% of Millennials would opt to pay a ransom or already have paid one in the past.
To support that, let us present one more study. This time, LastPass studied people’s online behaviors regarding passwords. It revealed that from Baby Boomers to Gen Z, people approach their digital safety and security differently. They found that despite being exposed to technology at an early age, Gen Z is least concerned with their security. On the contrary, Millennials and Baby Boomers are most concerned about their online safety and take extra measures to ensure their digital security.
Not only are the various generations’ use of technology and approaches to digital security different, the threats awaiting them in the digital world also differ. Since they all act in a distinct fashion, they are vulnerable to different types of online safety threats. For example, for teenagers and young adults, currently Gen Z and Alpha, one of the biggest threats is cyberbullying. Older generations face financial abuse, identity theft and other security attacks. Their knowledge on the topic also varies, making them more or less vulnerable to digital threats.
Kids from the age of 3 use devices to watch videos, while our elders use them to stay connected to their families. And for everyone in between, whether it be a Millennial or a Baby Boomer, online behaviors are different, and it is evident that there are different digital security approaches. However, whether you are a security expert or a basic user, without the proper protection and education, you may fall prey to malicious actors on the internet at any time.
It becomes evident that there is no one approach to digital security that fits all. Whether it is one’s personal security, privacy and safety, or an approach taken by a business, the solution is not set. Personalized protection, however, is not always possible. Everyone’s needs are different, and to cater to all would be virtually impossible. Some people and businesses prefer to have somewhat greater or less control over their protection, while others prefer to not be disturbed by it at all. Perhaps the easiest solution in situations like that is to have protection that you don’t have to think about at all. A silent knight protecting your digital world at all times.
One way for customers to procure that is when their Telco or ISP takes direct care of their protection, so they don’t even have to think about it. A solution like this can be incorporated into an ISP or Telco product offering, for example, ESET NetProtect. This security approach can give customers peace of mind, knowing their provider is taking care of their digital security on their behalf.
ESET NetProtect is not only easy to integrate, but also a great addition to a sales plan. Its reputation builds on its easy integration into existing Telco or ISP service offerings, while delivering full-service protection against malware, loss of privacy and phishing on all personal devices. NetProtect makes safe and secure browsing a matter of course. This offering keeps devices safe and online browsing safe from suspicious domains and websites. It also has a filter that allows you to blacklist domains and content categories based on user preference.
And above all, this product runs on your device, without you having to worry about it. Its user-friendly management with a range of settings ensures your overall satisfaction.
by Alžbeta Kovaľová, ESET