
The latest version of Bandook steals sensitive documents and credentials from corporate networks, creates a malicious Chrome extension, and misuses URL shorteners like Rebrandly and Bitly.
ESET Research has recently uncovered a new and still active campaign that uses more advanced versions of the old crimeware Bandook to spy on its victims. The ongoing campaign is targeting corporate networks in Spanish-speaking countries, with 90% of ESET telemetry detections in Venezuela. ESET researchers have found new functionality and changes to Bandook. Because of the malware used and the targeted locale, ESET chose to name this campaign Bandidos.
ESET has seen more than 200 detections for the malware droppers in Venezuela in 2021; however, a specific vertical targeted by this malicious campaign could not be identified. According to telemetry data, the main interests of the attackers are corporate networks in Venezuela: some in manufacturing companies, and others in construction, healthcare, software services, and even retail. Given the capabilities of the malware and the kind of information that is exfiltrated, it seems that the main purpose of Bandidos is espionage.
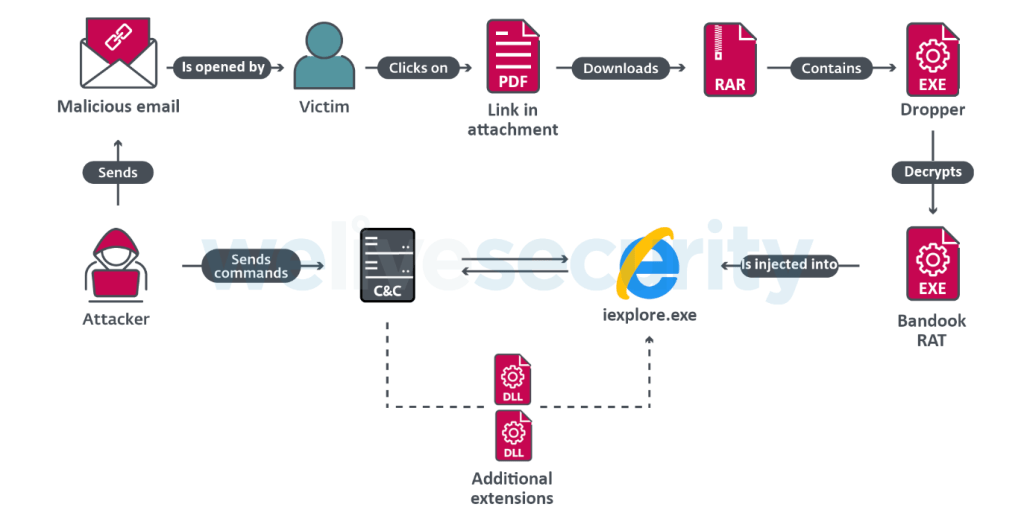
The prospective victims receive malicious emails with a PDF attachment. The PDF file contains a link to download a compressed archive and the password to extract it. Inside the archive there is an executable file: a dropper that injects Bandook into an Internet Explorer process. The attackers use URL shorteners such as Rebrandly or Bitly in their PDF attachments. The shortened URLs redirect to cloud storage services such as Google Cloud Storage, SpiderOak, or pCloud, from where the malware is downloaded. The main purpose of the dropper is to decode, decrypt, and run the payload and to make sure that the malware persists in a compromised system.
“Especially interesting is the ChromeInject functionality,” says Fernando Tavella, an ESET researcher who investigated the Bandidos campaign. “When the communication with the attacker’s command and control server is established, the payload downloads a DLL file, which has an exported method that creates a malicious Chrome extension. The malicious extension tries to retrieve any credentials that the victim submits to a URL. These credentials are stored in Chrome’s local storage.”
Bandook is an old remote access trojan. There are references to it being available online as early as 2005, though its use by organized groups was not documented until 2016. In 2016, it was reportedly used to target journalists and dissidents in Europe. Then, in 2018, it was used to attack new targets, such as educational institutions, lawyers, and medical professionals. Finally, in 2020, it was seen in attacks against multiple sectors, including government, financial, IT, and energy.
“Previous reports have mentioned that the developers of Bandook might be developers for hire, which makes sense given the various campaigns with different targets seen through the years. We must note, however, that in 2021 we have seen only one active campaign: the one targeting Spanish-speaking countries that we document here. It shows though that it is still a relevant tool for cybercriminals,” opines Matías Porolli, an ESET researcher who worked on the analysis with Tavella.
