ESET researchers published today another installment in their ongoing series of Latin American banking trojans. Since 2018 they have investigated Vadokrist, a trojan that is specifically focused on Brazil. The malware utilizes backdoor functionality and is distributed via malicious spam emails targeting financial institutions.
Unlike most other Latin American banking trojans, Vadokrist does not collect information about victims immediately after successfully compromising their machines. Nevertheless, based on ESET analysis, Vadokrist seems to share several important features with Amavaldo, Casbaneiro, Grandoreiro, and Mekotio – other Latin American banking trojans described earlier in the research series.
“The vast majority of Latin American banking trojans collect information about the victim’s machine when first run. The only information Vadokrist collects is the victim’s username, and it does so only after initiating an attack on a targeted financial institution,” says ESET researcher Jakub Souček, coordinator of the team that analyzed Vadokrist.
“Despite its lack of capability to collect information, Vadokrist can manipulate the mouse and simulate keyboard input, log keystrokes, take screenshots, and restart the machine. It is also able to prevent access to banking websites by killing the browser process, which we believe is a technique to prevent victims from accessing their online bank accounts, aiding the attackers in retaining control,” explains Souček.
For more technical details about Vadokrist, read the blog post “Vadokrist – A wolf in sheep’s clothing” on WeLiveSecurity. Make sure to follow ESET Research on Twitter for the latest news from ESET Research.
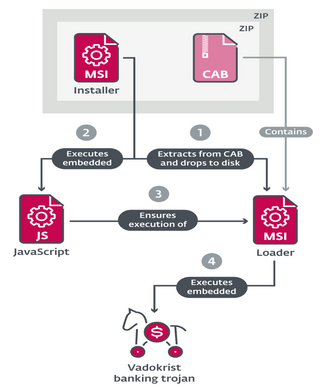
Execution chain recently used by Vadokrist