Making a little effort to understand the most common threats when choosing and handling your cryptocurrency wallet can help secure your crypto-assets in the long run.
When it comes to facing diverse threats, not every cryptocurrency wallet is the same. Each wallet is designed differently — to balance security with ease of use, privacy and other requested features, which always works against security. The security of your chosen wallet is very much the result of the robust nature (or lack) of its underlying code, which prompts the question, “How well did the developers adhere to security by design principles when building the wallet?”
Furthermore, the security-related practices of your wallet’s supply chain, including your selected wallet provider, along with the cryptocurrency exchange you use, the evolving cyber-threat environment and your cyber-hygiene habits combined, bring a lot to bear on overall security. While these considerations are relevant to all software and devices, users may appreciate their importance most acutely with respect to their own use of financial applications and their “money.”
Here, I focus on hot and cold wallets, the threats surrounding their use and some recommendations.
Enhanced privacy for cryptocurrency wallet users benefits security
It should be made clear that unlike the classic leather wallet, a cryptocurrency wallet does not actually store your money. Rather, a wallet holds the private key that lets you control your virtual coins and tokens for making transactions in a blockchain.
Many wallets use a hierarchical deterministic (HD) framework for managing keys and wallet addresses. In this framework, a unique master seed is used to generate multiple public-private key pairs along with wallet addresses so that a different address can be used each time you make a transaction.
By constantly transacting with a different wallet address, it becomes more difficult for anyone looking at the relevant blockchain to associate all your transactions back to a single source, thus enhancing privacy. While the gain in privacy has a positive effect for security, taken alone it is not enough for security.
Hot wallets connected to today’s computer ecosystems — a lot of trust needed
When Binance suffered a hack of one of its hot wallets in May 2019, crypto traders on the platform lost up to a combined total of 7,000 bitcoins along with multifactor authentication (MFA) codes and API keys. The loss of MFA codes is particularly damaging for the protection of users and carries a potentially high cost to companies when on occasion it isn’t enough to protect data. Fortunately for its clientele, Binance had the year before set up the Secure Asset Fund for Users — a fund that collects 10 percent of all trading fees into a cold wallet, from which to reimburse victims of such a successful attack.
This hack also demonstrates how a weak point of a hot wallet resides precisely in its “always connected to the internet” status. Hot wallets are tight-knit participants of today’s computer ecosystems subject to the same threats and need for caution.
This means that threats to wallets can leverage the usual bad habits of internet users — reusing easy-to-guess passwords, carelessly clicking on links, failing to perform updates or downloading “free” software via torrents — and deploy the typical malware designed to steal, like fake apps, keyloggers and clippers.
Clippers: your clipboard under attack
A clipper is a type of malware that secretly replaces the content of the clipboard to take advantage of the very common copy and paste action. With this strategy, the copied content, say, your wallet address, is replaced with ill-intentioned content — the attacker’s wallet address — when you paste.
The first Android clipper ever detected in the Google Play store — Android/Clipper.C — was posing as an app called MetaMask, a platform for accessing the decentralized apps built on the Ethereum blockchain. Android/Clipper.C swapped out Bitcoin and Ethereum wallet addresses copied to the clipboard with ones belonging to the attackers.
The same trick, which went undetected for years, was used by a trojanized version of the Tor Browser. Privacy-concerned users who were deceived into downloading this trojanized Tor Browser on their Windows machines had their Bitcoin wallet addresses being surreptitiously replaced whenever they visited particular darknet markets to make transactions. This allowed the operators of this malware to steal at least 4.8 bitcoins.
Fake login pages — you could’ve fooled me!
It is not unusual for malicious developers to supply mobile wallet versions of popular desktop wallet apps or for well-known cryptocurrency exchanges. The idea behind these types of malicious campaigns is to fill the gap left behind by the familiar brand names in crypto and attract more potential victims. In the case that a legitimate mobile app is already offered by a brand, the fake version of the app attempts to steal customers who are looking for the real deal but who likely lack awareness of such a scam.
Victims who download one of these fake cryptocurrency wallet apps are often presented with a login page that is phishing for private keys or mnemonic phrases. With even one of these pieces of information in hand, the malicious operators can quickly gain control over your wallet. Some variants of the fake MyEtherWallet app, for example, even “double phished” for both items in sequence — just to make sure.
Another ploy used by these fake apps is to present victims with a public key for “your” new wallet, presented as copiable text and/or a scannable QR code. Instructions are simple: “Send your coins into your new wallet!” The catch is you don’t have the private key — the operators of the malware do. After the transfer, say goodbye to your coins.
Some phony apps up the ante by offering wallets that “manage” multiple cryptocurrencies for trading in an exchange — a perfect ruse to dip into more than one of your wallets. The fake Trezor Mobile Wallet, for example, offered one wallet for each supported cryptocurrency — 13 wallets in total — presenting victims with multiple public keys to “cover their diverse crypto needs.”
There are malicious mobile apps that attempt to overlay fake login screens on legitimate wallet or other financial apps. Luckily, via Banking & Payment Protection, ESET Mobile Security prevents apps from overlaying the screens of your financial apps. Of course, the tricks employed with fake mobile apps apply equally across the board to fake desktop apps, as well as phishing sites made to appear like real login pages to your favorite online wallet.
We looked at some of the threats surrounding the use of hot wallets, specifically, clippers and fake login pages. These threats are particularly lethal due to the fact that hot wallets are always connected to the internet. Here, I continue my overview of the cryptocurrency wallet threat landscape by taking a look at malware-laced links as another top danger to hot wallet users, along with some security considerations relevant for cold wallet users.
Bad links and more bad links
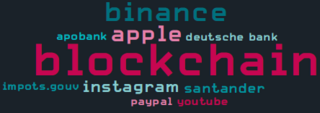
Have you ever clicked on a link that looked like “blockchain.com” but turned out to be something else? This is called a homoglyph attack. By replacing certain characters in the domain name with ones that either look similar or identical to human eyes (but are actually different to computers), phishing operators can craft links that appear to lead to popular websites that actually resolve to malicious sites. ESET telemetry for Q2 2020 showed attackers were focusing on cryptocurrency exchanges with blockchain.com and binance.com being the most targeted domains:
Without a security solution like ESET Internet Security installed on my machine, or short of a detective’s eye for picking up on the character switch — a highly unlikely event — nothing would stop me from getting phished.
Phishing can also happen via another, very typical path — spam emails attempting to clog my inbox. Clicking on malicious links in these spam messages and potentially giving banking trojans, such as Mekotio, a chance to do damage on my PC is quite unwelcome. Some variants of Mekotio, for example, attempt to steal bitcoins by replacing the bitcoin wallet address in the clipboard.
If I never copy and paste my wallet address, well, a keylogger is standard equipment for a lot of malware. So again, if it weren’t for my Banking & Payment Protection, packaged as part of my ESET Internet Security solution for protection against keyloggers, I would have much less confidence when typing in my wallet address via a browser.
Before leaving the topic of bad links, if you are still using torrents to download cracked or pirated software and games and then switching over to an exchange to do a little crypto trading, think again. As one more deterrent against the use of torrent sites, malware like KryptoCibule is found on some of these platforms. KryptoCibule tries to hijack cryptocurrency transactions by replacing wallet addresses in the clipboard and exfiltrating any cryptocurrency-related files it finds on the victim’s machine.
Cold wallets — limiting the threats to a physical playing field
As the more well-versed crypto traders are aware, the best way to minimize the dangers that beset the use of hot wallets is to use a cold wallet. Two popular options are Ledger and Trezor. By creating an air gap between your wallet and the internet, the risks take on a predominantly physical outlook.
There is the obvious risk of losing your cold wallet, having it stolen or, less likely but possible, tampering occurring along the supply chain. Then, in the hands of knowledgeable hardware hackers, both Trezor and Ledger have been coaxed to give up the key and recovery phrase.
While using cold wallets decreases numerous cyber risks, the parallel decrease in ease of use can still remain a bit of a sore tooth for some. And our “friendly” malware operators have just the solution to soothe that pain — Google Chrome extensions and Firefox add-ons that integrate your Ledger wallet with the browser. So, back to the world of hot wallets.
“Now, you can access wallet functionality directly from your browser to quickly and easily make cryptocurrency transactions. All you have to do is share your 12/24-word recovery phrase to sign up.” You can easily guess the glib words that these hackers might use to persuade potential victims.
After sharing your recovery phrase, the attackers can quickly clone your hardware wallet and take over your crypto-assets. Total losses for this type of scam exceed $250,000, according to some reports. ESET detects these threats as JS/ExtenBro.CryptoSteal.
Recommendations
- Keep your devices updated and always use a reliable security solution, such as ESET Internet Security or ESET Mobile Security, to protect them from the latest threats.
- If you’d like to download a cryptocurrency wallet app, first make sure your selected service really offers a mobile, desktop or online wallet by checking the service’s official website.
- When downloading mobile wallet apps from Google Play, review the number of downloads, the app ratings and reviews. Be cautious of newly published apps with positive reviews that seem too good to be true.
- Where the option is available, always use multifactor authentication to protect your wallet accounts with an extra layer of security.
- Think twice about where you are sharing your wallet recovery phrase and key.
- Type your wallet address, instead of copying and pasting it, and double-check the address before using it.
- Determine whether the app provider offers insurance/consumer protection against coin losses.
Considering e-trading? Many of these practices are relevant there too. Have a read about e-trading and the wider use of FinTech apps.
written by Rene Holt, ESET

