
Scams demanding bitcoin on pain of infecting you with the coronavirus gain their fair share of shine among schemes with a thin veneer of plausibility.
We’ve already warned you about all manner of spammers and scammers using strategies based on interest in, or fear and concern about, coronavirus and its associated disease, COVID-19.
Not to be outdone, some of the various ransomware gangs have suddenly developed a semblance of conscience, publicly announcing that they will avoid targeting healthcare providers for the duration of the pandemic, though whether or not their promises can be trusted is a subject for a separate discussion.
Many weeks into the outbreak, coronavirus and the world’s response to its pandemic disease still enjoy wall-to-wall coverage on cable news. The global crisis leads, even dominates, most other news bulletins, being a topic for which many have an apparently unquenchable thirst. Hence, even the most unimaginative and slothful wannabe cybercriminals are repackaging their own or others’ scams and shysterism in COVID-19 wrappers.
Herein we document a couple more coronavirus-related cyber-scams that you shouldn’t be shocked to see in your inbox…
Shut up and dance (coronavirus cut)
We have previously documented contemporary sextortion scams, in which a threat is received that typically indicates someone has hacked the recipient’s computer, recorded (via the webcam) them watching pornography and made a side-by-side video of the porn and the webcam recording. This purported hacker also claims to have all the contacts from the recipient’s email and social media, and threatens to send them all a link to that video if the recipient doesn’t cough up some bitcoin. However, if a payment is made, supposedly this pillar of society is to be trusted to not distribute the video at all and to delete it (rather than to threaten the victim again, unless they pay again, ad nauseam…).
So, what happens when a global pandemic strays into a sextortion scammer’s purview? The example in Figure 1, perhaps?
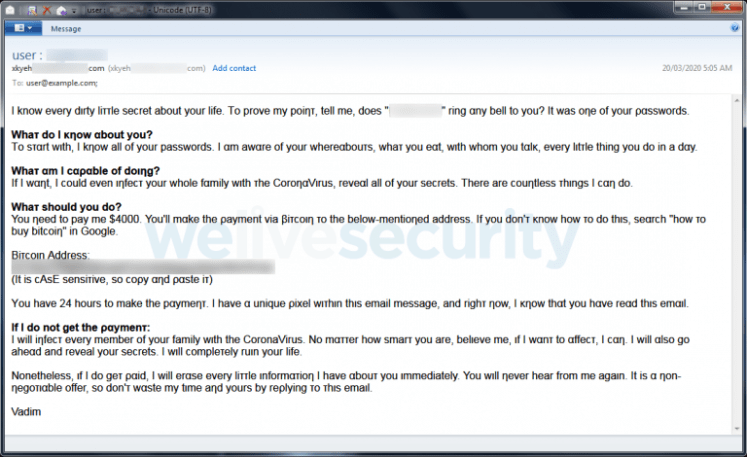
Aside from the usual twist on the plot of the Black Mirror episode referenced in this section’s subheading, you get a side serving of threatened criminal transmission of a disease. This scam email is also interesting as it continues the tactic of pairing passwords found in publicly leaked account compromises to the recipients’ email addresses in the hope that makes its extortion messages more convincing. It is also interesting for randomly replacing characters in the message with Unicode homoglyphs (characters that are similar to, if not indistinguishable from, the originals). A few characters in Figure 1 should seem a bit odd, but the full extent of this replacement (and how convincing carefully chosen homoglyphs can be) is illustrated in Figure 2, where all these replacements are highlighted.

In case any readers have received a sextortion scam email with the additional threat of infecting you or your family with coronavirus, as seen here, rest assured: the scumbags behind this threat are far too lazy to shower regularly, much less drag their sorry backsides out of their parents’ basements, and would have no idea of how or where to obtain suitable COVID-19 samples, much less be able to weaponize and deliver them.
Dumb and dumber
As improbable as the preceding sextortion scam’s threat to infect the recipient with coronavirus might seem, the perpetrators of the next example were clearly even less enthused about setting up their scam. Laziness or ignorance – you decide after reading the message in Figure 3…

It seems to me that for an extortion scam to work, the threat must be at least vaguely credible, but how is this threat supposed to work? What is the reputed, anonymous neighbor going to do to infect you? Sneak over after dark and cough on your letterbox and exterior door handles?
Regardless, this is probably the weirdest extortion scam email I’ve ever seen. The threat is almost subliminal and no conditions are put on paying the extortionist – no due date, nor a required amount. “I might try to make you sick with this virus that’s killing me. Give me money” is what it boils down to. Perhaps the perpetrator is counting on enough recipients (even just a few) already being so worried or scared that they voluntarily hand over more than the cost of the spam run that delivered these messages?
Closing comments
Neither of the bitcoin addresses seen in the samples above, nor a couple of other bitcoin addresses from other instances of these scams found online, had received any payments of note when last checked (one had received a single payment of a tiny fraction of a bitcoin, equivalent to about US$0.04 – yes, four cents). So, these don’t seem like particularly lucrative scams, but they risk spreading further worry and fear at this time of heightened concern, which may be damaging enough.
If you happen to see emails similar to the examples above, just delete them, and please stay safe – and healthy!
written by Nick FitzGerald, Senior Research Fellow at ESET
