The company is rushing to fix a glitch that may let other iPhone users hear and see you – before you answer the call.
Apple has promised to issue a software update later this week to fix a serious bug in Apple’s video and audio call app FaceTime that can be easily exploited to spy on people, according to a 9to5Mac report.
This is after another report on the site revealed late on Monday that the glitch allows any iPhone user to video-call another iPhone user via FaceTime and listen in on the audio on the other end – before the recipient has accepted or rejected the incoming call.
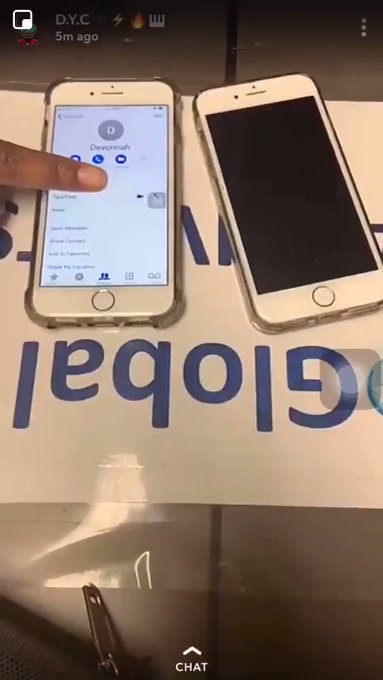
How does it work? In short, the caller would initiate a FaceTime call and immediately afterwards launch the app’s group calling feature by tapping on ‘Add person’ and adding their own phone number. That’s all it takes to trick FaceTime into believing that the recipient has just answered the ‘conference call’, enabling the caller to hear the audio on the other end – unbeknownst to the victim.
Meanwhile on the screen of the victim’s device, it would appear as if the phone were still ringing with the FaceTime request.
That’s not all. While it was first believed that ‘only’ the audio can be exposed, BuzzFeed News later wrote that the bug can apparently also expose the front-facing video camera of the recipient’s handset. If the recipient dismisses or silences the incoming FaceTime conference call by pressing the power button or one of the volume controls, their handset will also begin to send live video. Again, this happens with zero awareness on the victim’s part.
This ‘hack’, simple to the point of being bizarre, can also be done when making a FaceTime call from an iPhone to a Mac computer. According to CNN, the bug affects iPhones and iPads running iOS 12.1, which introduced Group FaceTime, but also impacts computers running macOS Mojave.
The issue has attracted the attention of Governor of New York Andrew M. Cuomo, who called the bug “an egregious breach of privacy”.
The Verge reports that Apple’s disabling of Group FaceTime has largely fixed things while the software update is in the works. If that doesn’t ease your concerns, however, you may want to deactivate the app until Apple delivers the update.
written by Tomas Foltyn, ESET We Live Security