
2016 brought some interesting developments to the Android ransomware scene, seeing ransomware emerge as one of the most pressing cybersecurity issues on the mobile platform. Authors of lock-screen ransomware, as well as file-encrypting “crypto-ransomware”, used copycat techniques proven effective in desktop malware, as well as develop their own sophisticated methods specifically designed for Android users.
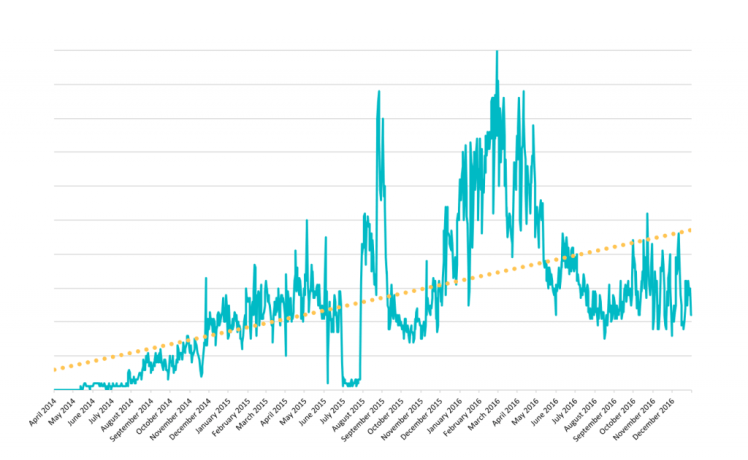
With more and more consumers switching from PC to mobile, the devices are used to store increasing amounts of valuable data, making Android ransomware ever more worthwhile for attackers. According to ESET LiveGrid®, the number of Android ransomware detections has grown in year on year comparisons by more than 50%, with the largest spike in the first half of 2016.
Among the most dominant tactics used by cybercriminals, lock-screen “police ransomware” has continued to prove its place as the go-to means of scaring victims into paying up. Apart from observing gradual improvements in features of Android ransomware, ESET researchers have also seen cybercriminals put increased effort into keeping a low profile by encrypting and burying the malicious payload deeper into the infected apps.
Target-wise, Android ransomware operators have been shifting their focus from Eastern European to US mobile users. However, last year also demonstrated an increased activity on the Asian market. This could be seen in the Jisut lock-screen with its localized Chinese ransom message and doubled detections in the previous 12 months.
To find out more about ransomware on Android, its current trends and most noteworthy examples since 2014, read the newly released whitepaper by ESET.
by Ondrej Kubovic, ESET We Live Security

15 thoughts on “Trends in Android ransomware”