
As of February 13th, 2017, Gmail has started deploying their new restrictive policy on .js file attachments, extending their list of file types blocked for security reasons. After the full release, Gmail users won’t be able to send or receive mail containing .js attachments, even if they’re in a compressed and archived form.
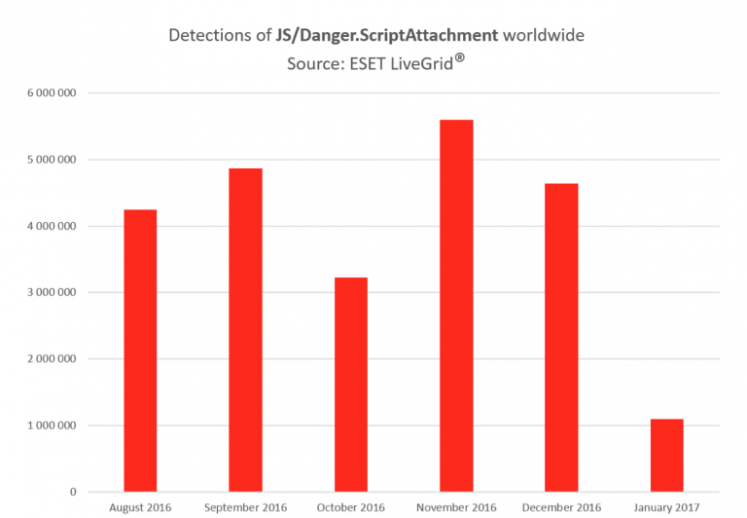
Seeing that JavaScript attachments have proven to be one of the most popular ways for cybercriminals to spread their malicious work worldwide, this is good news. Only in the past six months, ESET LiveGrid® has recorded tens of millions detections of JS/Danger.ScriptAttachment, which is ESET’s detection name for malicious .js script spreading via email attachments.
Detected under the name are malicious scripts aiming to infect the device with different types of malware chosen by the attackers. Apart from various ad-clickers and banking malware, the most prevalent type of infection among the recent detections has been the much-feared crypto-ransomware, including the notorious families Locky, TorrentLocker and Crysis.
Although the change is likely to positively affect the safety of online communication worldwide, cybercriminals are known to be inventive when it comes to finding loopholes in security measures. With .js attachments blocked by one of the dominant webmail providers, attackers will most likely start looking for alternative ways into devices of their potential victims.
Just like Google advises Gmail users to use their storage solutions to share .js files used for legitimate reasons, also cybercriminals might start abusing those more frequently and lure users into clicking on corresponding links instead of opening attachments (as they did, for instance, when spreading another infamous ransomware Petya).
So while essentially good news, the update should also be a signal for users to consider these potential alternatives and pay extra attention to emails linking to third party storage services.
by Peter Stancik, ESET We Live Security
