Ransomware is being increasingly relied upon in cyberattacks, according to Verizon’s latest Data Breach Investigations Report.
Over the last 12 months, there has been a 16% increase in ransomware attacks, the authors of paper stated.
This was touched upon recently by ESET’s Ondrej Kubovič in a previous article.
He said how this type of attack is a highly topical subject because of the types of organizations being targeted – for examples, hospitals – and because of how prevalent ransomware has become.
The report also revealed that 89% of all attacks “involve financial or espionage motivations”, with the former a clear catalyst.
Interestingly, the study noted how phishing is a growing concern, as it’s evident that a lot of people are not familiar with this tactic.
For example, Verizon found that 30% of phishing messages were opened in 2015, which is up by a massive 23% from 2014.
Phishing has been used by cybercriminals for years to access personal information. It can manifest itself as an email, text message or even a website.
“You might say our findings boil down to one common theme – the human element,” explained Bryan Sartin, executive director of global security services at Verizon Enterprise Solutions.
“Despite advances in information security research and cyber detection solutions and tools, we continue to see many of the same errors we’ve known about for more than a decade now. How do you reconcile that?”
The authors of the report were also keen to highlight what they describe as a “three-pronged attack”, which is “being repeated over and over again” by cybercriminals.
It begins with a phishing email that comes with a link to either a corrupted website or attachment.
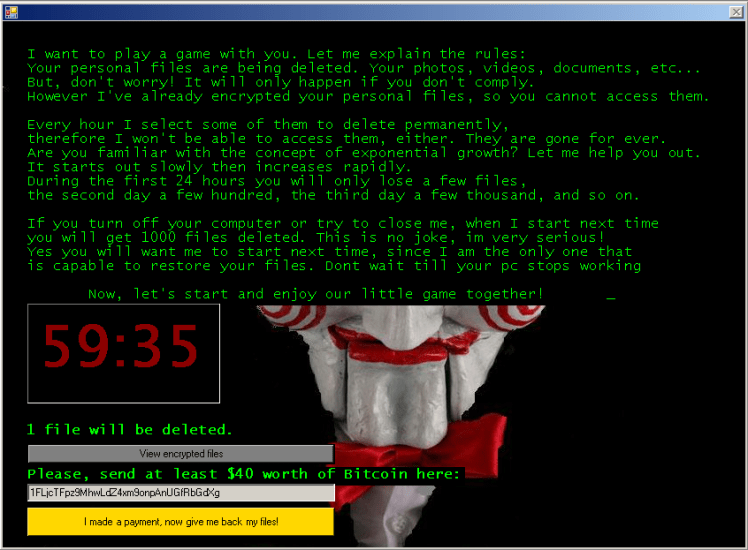
On clicking through to a website or attachment, malware is downloaded onto a victim’s computer.
This “establishes an initial foothold”, meaning that further malware can be downloaded to either encrypt data, access information and/or steal credentials.
Finally, these credentials are used to carry out further cybercriminal activity, including breaching bank accounts.
“This year’s report once again demonstrates that there is no such thing as an impenetrable system,” added Mr. Sartin.
“But often times even a basic defense will deter cybercriminals who will move on to look for an easier target.”
by Narinder Purba, ESET We Live Security
