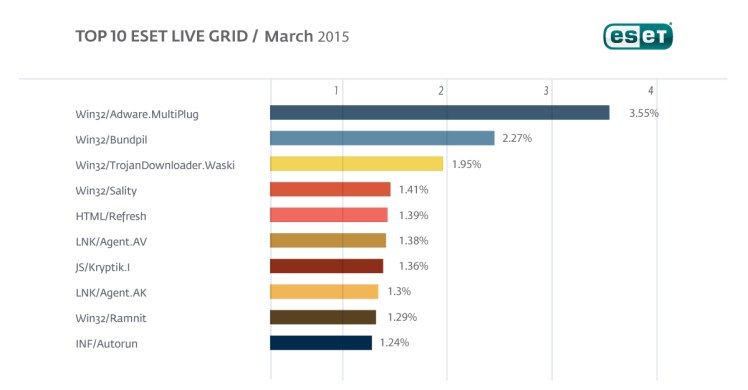
The Top Ten Threats of March 2015
1. Win32/Adware.MultiPlug
Previous Ranking: 1
Percentage Detected: 3.55%
Win32/Adware.Multiplug is a Possible Unwanted Application that once it gets a foothold on the users system might cause applications to display pop-up advertising windows during internet browsing.
2. Win32/Bundpil
Previous Ranking: 3
Percentage Detected: 2.27%
Win32/Bundpil.A is a worm that spreads via removable media. The worm contains an URL address from which it tries to download several files. The files are then executed and HTTP is used for communication with the C&C to receive new commands. The worm may delete the following folders:
*.exe
*.vbs
*.pif
*.cmd
*Backup.
3. Win32/TrojanDownloader.Waski
Previous Ranking: 5
Percentage Detected: 1.95%
Win32/TrojanDownloader.Waski is a Trojan that uses HTTP to try to download other malware. It contains a list of two URLs and tries to download a file from the addresses. The file is stored in the location %temp%\¬miy.exe, and is then executed.
4. Win32/Sality
Previous Ranking: 7
Percentage Detected: 1.41%
Sality is a polymorphic file infector. When executed registry keys are created or deleted related to security applications in the system and to ensure that the malicious process restarts each time the operating system is rebooted.
It modifies EXE and SCR files and disables services and processes implemented by and associated with security solutions.
More information relating to a specific signature: http://www.eset.eu/encyclopaedia/sality_nar_virus__sality_aa_sality_am_sality_ah
5. HTML/Refresh
Previous Ranking: 2
Percentage Detected: 1.39%
HTML/Refresh is a Trojan that redirects the browser to a specific URL location with malicious software. The program code of the malware is usually embedded in HTML pages.
6. LNK/Agent.AV
Previous Ranking: 8
Percentage Detected: 1.38%
LNK/Agent.AV is a link that concatenates commands to execute legitimate code while running the threat code in the background. It is similar in its effect to the older autorun.inf type of threat.
7. JS/Kryptik.I
Previous Ranking: 4
Percentage Detected: 1.36%
JS/Kryptik is a generic detection of malicious obfuscated JavaScript code embedded in HTML pages; it usually redirects the browser to a malicious URL or implements a specific exploit.
8. LNK/Agent.AK
Previous Ranking: N/A
Percentage Detected: 1.30%
LNK/Agent.AK is a link that concatenates commands to execute legitimate code while running the threat code in the background. It is similar in its effect to the older autorun.inf type of threat. This vulnerability became known at the time of discovery of Stuxnet, as it was one of four vulnerabilities that were executed by Stuxnet variants.
9. Win32/Ramnit
Previous Ranking: 9
Percentage Detected: 1.29%
This is a file infector that executes every time the system starts. It infects .dll (direct link library) and .exe executable files and also searches htm and html files so as to insert malicious instructions into them. It exploits a vulnerability (CVE-2010-2568) found on the system that allows it to execute arbitrary code. It can be controlled remotely to capture screenshots, send information it has gathered, download files from a remote computer and/or the Internet, and run executable files or shut down/restart the computer.
10. INF/Autorun
Previous Ranking: 10
Percentage Detected: 1.24%
INF/Autorun is a generic detection of versions of the autorun.inf configuration file created by malware. The malicious AUTORUN.INF file contains the path to the malware executable. This file is usually dropped into the root folder of all the available drives in an attempt to auto-execute a malware executable when the infected drive is mounted. The AUTORUN.INF file(s) may have the System (S) and Hidden (H) attributes present in an attempt to hide the file from Windows Explorer.