At the end of April Microsoft has announced that a vulnerability in Word was actively being exploited. This vulnerability occurred in parsing RTF files and it was assigned as CVE-2014-1761. We have since seen several cases where this exploit is used to deliver malware. We found one particularly interesting, as it contained a new variant of MiniDuke (also known as Win32/SandyEva).
MiniDuke was first discussed by Kaspersky in March 2013 . Some of the characteristics of MiniDuke — such as its small size (20 KB), its crafty use of assembly programming, and the use of zero-day exploits for distribution — made it an intriguing threat. Although the backdoor is still quite similar to its previous versions, some important changes were made since last year, the most notable being the introduction of a secondary component written in JScript to contact a C&C server via Twitter.
The exploit document was named Proposal-Cover-Sheet-English.rtf and when compared to the documents that were used in 2013, which were of a political nature, it is quite bland. We have received the document on April 8th, only three days after the compilation of the MiniDuke payload, which was dated April 5th in the PE header. The payload still remains quite small at only 24 KB.
The functionality of the shellcode which is executed by triggering the vulnerability is rather simple and straightforward. After decrypting itself and obtaining the addresses of some functions exported by kernel32.dll, it decrypts and drops the payload in the %TEMP% directory in a file named “a.l” which is subsequently loaded by calling kernel32!LoadLibraryA.
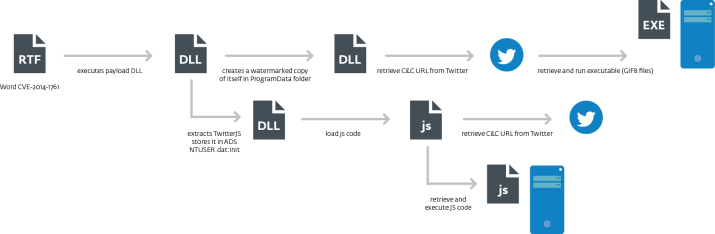
The graph presents the execution flow of this malware, if the exploitation is successful. This version of MiniDuke payload comes with two modules, which we refer to as the main module and the TwitterJS module.
Once MiniDuke receives control, it checks that the host process is not rundll32.exe and whether the current directory is %TEMP%. If either of those conditions are met, the malware assumes it is run for the first time and it proceeds with the installation on the system. MiniDuke gathers information about the system and encrypts its configuration based on that information. The end result is that it is impossible to retrieve the configuration of an encrypted payload if analyzing it on a different computer.
As the next step, MiniDuke gathers the following information from the infected systems:
- computer name and user domain name
- country code of the infected host IP address obtained from http://www.geoiptool.com
- OS version information
- domain controller name, user name, groups a user account belongs to
- a list of AV products installed onto the system
- Internet proxy configuration
- version of MiniDuke
This information is then sent to the C&C server along with the request to download a payload. In the event that MiniDuke is unable to retrieve a C&C URL from this account, it generates a username to search based on the current date. The purpose of this script is to use Twitter to find a C&C and retrieve JScript code to execute. It first generates a Twitter user to search for; this search term changes every 7 days and is actually a match to the real account name, not the Twitter account name.
We generated the list of Twitter search terms for 2013-2014 and checked if any of those were registered. At the moment only one exists, @AA2ADcAOAA, which is the TwitterJS account that was generated between August 21st and 27th 2013. This account has no tweets. In an effort to discover potential victims, we registered the Twitter accounts corresponding to the current week both for the main and TwitterJS components and set up tweets with encrypted URLs so that an infected computer would reach out to our server. So far we have received connections via the TwitterJS accounts from four computers located in Belgium, France and the UK. We have contacted national CERTs to notify the affected parties. We detect the RTF exploit document as Win32/Exploit.CVE-2014-1761.D and the MiniDuke components as Win32/SandyEva.G.