The Top Ten Threats
1. Win32/Bundpil
Previous Ranking: 1
Percentage Detected: 2.9%
Win32/Bundpil.A is a worm that spreads via removable media. The worm contains an URL address, and it tries to download several files from the address. The files are then executed and the HTTP protocol is used. The worm may delete the following folders:
*.exe
*.vbs
*.pif
*.cmd
*Backup.
2. LNK/Agent.AK
Previous Ranking: 5
Percentage Detected: 1.86%
LNK/Agent.AK is a link that concatenates commands to run the real or legitimate application/folder and, additionaly runs the threat in the background. It could become the new version of the autorun.inf threat. This vulnerability was known as Stuxnet was discovered, as it was one of four that threat vulnerabilities executed.
3. Win32/Sality
Previous Ranking: 2
Percentage Detected: 1.67%
Sality is a polymorphic file infector. When run starts a service and create/delete registry keys related with security activities in the system and to ensure the start of malicious process each reboot of operating system.
It modifies EXE and SCR files and disables services and process related to security solutions.
More information relating to a specific signature: http://www.eset.eu/encyclopaedia/sality_nar_virus__sality_aa_sality_am_sality_ah
4. INF/Autorun
Previous Ranking: 4
Percentage Detected: 1.57%
This detection label is used to describe a variety of malware using the file autorun.inf as a way of compromising a PC. This file contains information on programs meant to run automatically when removable media (often USB flash drives and similar devices) are accessed by a Windows PC user. ESET security software heuristically identifies malware that installs or modifies autorun.inf files as INF/Autorun unless it is identified as a member of a specific malware family.
Removable devices are useful and very popular: of course, malware authors are well aware of this, as INF/Autorun’s frequent return to the number one spot clearly indicates. Here’s why it’s a problem.
The default Autorun setting in Windows will automatically run a program listed in the autorun.inf file when you access many kinds of removable media. There are many types of malware that copy themselves to removable storage devices: while this isn’t always the program’s primary distribution mechanism, malware authors are always ready to build in a little extra “value” by including an additional infection technique.
While using this mechanism can make it easy to spot for a scanner that uses this heuristic, it’s better to disable the Autorun function by default, rather than to rely on antivirus to detect it in every case.
5. Win32/Qhost
Previous Ranking: 9
Percentage Detected: 1.55%
This threat copies itself to the %system32% folder of Windows before starting. It then communicates over DNS with its command and control server. Win32/Qhost can spread through e-mail and gives control of an infected computer to an attacker.
6. HTML/ScrInject
Previous Ranking: 3
Percentage Detected: 1.54%
Generic detection of HTML web pages containing script obfuscated or iframe tags that that automatically redirect to the malware download.
7. Win32/Ramnit
Previous Ranking: 6
Percentage Detected: 1.27%
It is a file infector. It’s a virus that executes on every system start.It infects dll and exe files and also searches htm and html files to write malicious instruction in them. It exploits vulnerability on the system (CVE-2010-2568) that allows it to execute arbitrary code. It can be controlled remotley to capture screenshots, send gathered information, download files from a remote computer and/or the Internet, run executable files or shut down/restart the computer.
8. Win32/Conficker
Previous Ranking: 7
Percentage Detected: 1.26%
The Win32/Conficker threat is a network worm originally propagated by exploiting a recent vulnerability in the Windows operating system. This vulnerability is present in the RPC sub-system and can be remotely exploited by an attacker without valid user credentials. Depending on the variant, it may also spread via unsecured shared folders and by removable media, making use of the Autorun facility enabled at present by default in Windows (though not in Windows 7).
Win32/Conficker loads a DLL through the svchost process. This treat contacts web servers with pre-computed domain names to download additional malicious components. Fuller descriptions of Conficker variants are available at http://www.eset.eu/buxus/generate_page.php?page_id=279&lng=en.
While ESET has effective detection for Conficker, it’s important for end users to ensure that their systems are updated with the Microsoft patch, which has been available since the third quarter of 2008, so as to avoid other threats using the same vulnerability. Information on the vulnerability itself is available at http://www.microsoft.com/technet/security/Bulletin/ms08-067.mspx. While later variants dropped the code for infecting via Autorun, it can’t hurt to disable it: this will reduce the impact of the many threats we detect as INF/Autorun. The Research team in San Diego has blogged extensively on Conficker issues: http://www.eset.com/threat-center/blog/?cat=145.
It’s important to note that it’s possible to avoid most Conficker infection risks generically, by practicing “safe hex”: keep up-to-date with system patches, disable Autorun, and don’t use unsecured shared folders.
9. Win32/Dorkbot
Previous Ranking: 10
Percentage Detected: 1.1%
Win32/Dorkbot.A is a worm that spreads via removable media. The worm contains a backdoor. It can be controlled remotely. The file is run-time compressed using UPX. The worm collects login user names and passwords when the user browses certain web sites. Then, it attempts to send gathered information to a remote machine. This kind of worm can be controlled remotely.
10. Win32/TrojanDownloader.Waski
Previous Ranking: n/a
Percentage Detected: 1.02%
Win32/TrojanDownloader.Waski is a trojan which tries to download other malware from the Internet. It contains a list of two URLs and tries to download a file from the addresses. The HTTP protocol is used. The file is stored in the location %temp%\miy.exe, and is then executed.
Phishing Scam Update
by David Harley, ESET North America
by Urban Schrott, ESET Ireland
It may seem at the moment that I don’t write about anything apart from phishing scams and tech support scams. That’s not actually the case, but scammers don’t seem to take holidays, and a couple of things have come along that I couldn’t resist mentioning.
The first has the subject “RBS – Working to protect you and your card.” It appears to come from CreditCardOnlineServices(at)cards.rbs.co.uk.
RBS Credit Card Account Holder:
Your RBS Credit Card is designed to help keep you safe
Receive alerts when we spot a suspicious transaction
Sometimes we spot what looks like a fraudulent transaction on your credit card – so to make sure, we’ll call you and check. Better still, why not join our free fraud text alert service?
It’s just another way we’re working to keep your card and your money safe.
To sign-up for this service, simply visit our fraud text alert website.
Why is this interesting? Well, there are a couple of things here that indicate a scam.
- The giveaway absence of personalization – if you’re one of a financial institution’s customers, there’s no excuse for not addressing you by name and proving that they know something about you that a scammer wouldn’t.
- We’ve neutralized the link to the so-called text alert website, but it led to a site that had nothing to do with RBS or even the UK – it appeared to have a Swedish domain name – and actually contained other pages masquerading as other banks.
Apart from that – and the fact that I don’t have an RBS card! – there isn’t much here to indicate to the average user that it’s a scam. The English isn’t ‘foreign’ and does a good job of capturing the tone of a chatty advertising mailshot.
And here’s another one from ‘Lloyds’. Bizarrely, though at first sight the sender appears to be Lloyds Personal Banking, the actual mail address is toilet@ebay.com. It pays to check the mailbox address as well as the display name (Lloyds Personal Banking in this case), even though there’s no guarantee that the address used is a genuine address.
Resolving An Issue With Your Account
Dear Valued Customer
We need your help resolving an issue with your account. To give us to to work together on this, we’ve temporarily limited what you can do with your account until the issue is resolved.
How you can help
It’s usually pretty easy to take care of things like this. Most of the time, we just need a little more information about your account or latest transactions.
To help us with this and to find out what you can and can’t do with your account until the issue is resolved.click on the ink below to resolve issue
Log in here to resolve issue.
Sincerely,
Lloyds Bank
This one also lacks personalization and also links to a URL with no connection to Lloyds or the UK. The proofreader was a bit slack, too – “click on the ink below…” – and the English is a little more – well, unEnglish… Still, it’s noticeable that the scammer was aiming for the same chattier, more idiomatic style, and there’s some novelty to that.
Meanwhile, my colleague Urban Schrott has been writing for ESET Ireland about scams that have crossed his radar. While there’s no disputing the lengths Apple goes to defend its customers from security threats, it’s not possible for an operating system provider or security vendor to provide absolute protection for the user of any platform or security software from his own lack of caution. As Urban points out, if users are overconfident of the absolute security of their computing environment, “…that confidence can work against them when it comes to social engineering, particularly phishing, as they tend to trust “official” looking websites more [than they should] and cybercriminals know and abuse this to the maximum.
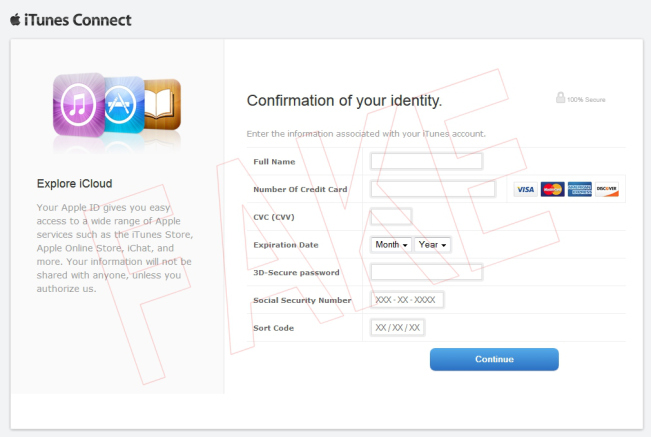
As an example, he describes how a very realistic looking phishing email is being received by Irish users, using the usual Apple visual clues and leading to a faked ITunes Connect login site at an address is that several security vendors have noted is associated with malware distribution, and which harvests users’ iTunes login details. He notes that it “still lets you in if you enter any made-up nonsense though.”
The prospective victim (addressed generically, of course, as ‘Dear Apple Customer’, is told that “in order to get back into your apple account, you’ll need to confirm your account. It’s easy: Click the link below to open a secure browser window. Confirm that you’re the owner of the account and then follow the instructions. .“
While the mail looks fairly realistic (with an Apple logo and so on) there are one or two details that you might have spotted. The failure to capitalize Apple; a couple of proofing errors (the unfortunate space between ‘account’ and the following period character, two period characters separated by a space character at the end of the paragraph; and the capitalized Click after a colon, which is common US usage, but not common in the UK or Ireland.
The fake iTunes Connect login is even more US-centric. Once “logged in”, the page asks you to “confirm” many of your personal details, including your credit card number and security code, your password and sort code, but also your Social Security number. Are there that many Americans in Ireland, I wonder?