Could that smartphone in your pocket be making money for cybercriminals?
Yes it could, and in this article we will explain how, using a real world example that has been targeting Android phones around the world. The use of smartphones is now very common in a wide range of countries. We carry them with us from the moment we wake up and we use them all day long. We use them to connect to the Internet, read emails, share information through social networks, to play video games and communicate with our friends and relatives.
With such a wide range of functionality, demand for these devices keeps rising, so an increasing number of new smartphones are being activated every day. This has become a profitable market not only for vendors and service providers, but also for cybercriminals who have started to target these platforms – not only to steal information from them, but also to use the mobile phone to make a profit by subscribing users to premium-rate numbers.
After several queries from users, the ESET Research Lab analysed the Boxer Trojan and discovered that the threat, detected by ESET Mobile Security as Android/TrojanSMS.Boxer.A
Once the malware was analysed and it was seen to be an SMS Trojan which uses commands to send SMS messages to premium-rate numbers, we were also able to identify Internet users asking about and claiming refunds for “mysterious” charges that had appeared in their invoices or accounts. In all these cases, the premium number causing this inconvenience was identified during the Boxer analysis.
SMS Trojans are classified as malicious programs for mobile phones whose main purpose is to subscribe the victim to premium-rate messaging numbers. This type of service usually informs the user that he has been successfully subscribed, but some Trojans in this category filter out SMS messages from those premium telephone numbers so that the user remains unaware of the infection; thus, while messages to and from other users or services are visible, messages connected to the premium-rate number are concealed. Potentially, this represents a serious financial problem for the user: if he or she fails to check their balance or account statement they could incur expensive charges.
The infographic shows the behavior of an SMS Trojan and how an attacker can gain advantage from it.
Basically, SMS Trojans cannot propagate themselves (unlike worms and viruses) so attackers need to hide the malicious code inside other applications such as video games or known applications.
Once the users are tricked into downloading and installing the infected app, their mobile phones are infected. When the user executes the infected app, an SMS is sent to a premium-rate number, activating a subscription for which the user will be charged.
The way in which premium-rate numbers work is very simple: they are activated by an SMS subscription message sent from the user’s mobile phone. The subscribed user receives SMS messages with content such as jokes or any other kind of data that can be sent through SMS. Every such message they receive will cost them some money.
Generally speaking, SMS Trojans have a limited range of actions, that is, they are only able to affect particular countries due to the fact that, in most cases, premium-rate numbers vary according to each operator and nation.
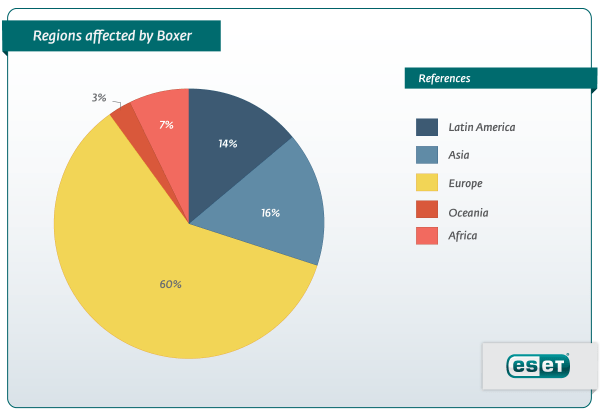
Despite this, Boxer has the ability to target victims in no less than 63 countries, from America, Europe, Africa, Asia and Oceania. (There could be many different reasons for this specific selection of countries and regions. Probably, as different variants have evolved, countries have been discarded and only the most profitable ones remain.) This targeting ability turns Boxer into an SMS Trojan with great propagation potential with a wide functional range.
Being able to target 63 different countries is one of Boxer’s most important characteristics so how is this possible? Every mobile phone stores information about which country and mobile network it belongs to. This information is known as MCC for Mobile Country Code and MNC, standing for Mobile Network Code. Once Boxer knows the country and mobile carrier to which the infected phone belongs, it will try to match it with the information stored inside the program and send an SMS to the ‘appropriate’ premium-rate service number to which to subscribe the victim.
Our observation of this family of malware confirms that cybercriminals are not only focusing their resources on the creation of increasingly complex malware for mobile devices, but that they are also starting to concentrate on how to expand the reach of their threats worldwide. It is likely that in the near future more malicious code targeting Android will be detected and we expect to find more examples of malware be constructed so as to affect users in as many regions as possible.
In order to avoid becoming a victim of this kind of threat we recommend that you:
- Install applications only from official markets such as Google Play, Apple Store, etc.
- Do not click on unknown links sent through email or SMS messages
- Use security software to prevent malicious code infecting your smartphone
We have a more technical post on this particular threat and also a detailed whitepaper on Boxer SMS Trojan (PDF). To protect your Android tablets and smartphones, you can use ESET Mobile Security for Android.
