The Top Ten Threats
1. INF/Autorun
Previous Ranking: 3
Percentage Detected: 6.36%
This detection label is used to describe a variety of malware using the file autorun.inf as a way of compromising a PC. This file contains information on programs meant to run automatically when removable media (often USB flash drives and similar devices) are accessed by a Windows PC user. ESET security software heuristically identifies malware that installs or modifies autorun.inf files as INF/Autorun unless it is identified as a member of a specific malware family.
Removable devices are useful and very popular: of course, malware authors are well aware of this, as INF/Autorun’s frequent return to the number one spot clearly indicates. Here’s why it’s a problem.
The default Autorun setting in Windows will automatically run a program listed in the autorun.inf file when you access many kinds of removable media. There are many types of malware that copy themselves to removable storage devices: while this isn’t always the program’s primary distribution mechanism, malware authors are always ready to build in a little extra “value” by including an additional infection technique.
While using this mechanism can make it easy to spot for a scanner that uses this heuristic, it’s better, as Randy Abrams has suggested in our blog (http://blog.eset.com/?p=94 ; http://blog.eset.com/?p=828) to disable the Autorun function by default, rather than to rely on antivirus to detect it in every case. You may find Randy’s blog at http://www.eset.com/threat-center/blog/2009/08/25/now-you-can-fix-autorun useful, too.
2. HTML/Iframe.B
Previous Ranking: 2
Percentage Detected: 4.84%
Type of infiltration: Virus
HTML/Iframe.B is generic detection of malicious IFRAME tags embedded in HTML pages, which redirect the browser to a specific URL location with malicious software.
3. HTML/ScrInject.B
Previous Ranking: 1
Percentage Detected: 4.09%
Generic detection of HTML web pages containing script obfuscated or iframe tags that that automatically redirect to the malware download.
4. Win32/Conficker
Previous Ranking: 5
Percentage Detected: 3.52%
The Win32/Conficker threat is a network worm originally propagated by exploiting a recent vulnerability in the Windows operating system. This vulnerability is present in the RPC sub-system and can be remotely exploited by an attacker without valid user credentials. Depending on the variant, it may also spread via unsecured shared folders and by removable media, making use of the Autorun facility enabled at present by default in Windows (though not in Windows 7).
Win32/Conficker loads a DLL through the svchost process. This threat contacts web servers with pre-computed domain names to download additional malicious components. Fuller descriptions of Conficker variants are available at http://www.eset.eu/buxus/generate_page.php?page_id=279&lng=en.
While ESET has effective detection for Conficker, it’s important for end users to ensure that their systems are updated with the Microsoft patch, which has been available since the third quarter of 2008, so as to avoid other threats using the same vulnerability. Information on the vulnerability itself is available at http://www.microsoft.com/technet/security/Bulletin/ms08-067.mspx. While later variants dropped the code for infecting via Autorun, it can’t hurt to disable it: this will reduce the impact of the many threats we detect as INF/Autorun. The Research team in San Diego has blogged extensively on Conficker issues: http://blog.eset.com/?cat=145
It’s important to note that it’s possible to avoid most Conficker infection risks generically, by practicing “safe hex”: keep up-to-date with system patches, disable Autorun, and don’t use unsecured shared folders. In view of all the publicity Conficker has received and its extensive use of a vulnerability that’s been remediable for so many months, we’d expect Conficker infections to be in decline by now if people were taking these commonsense precautions. While the current ranking looks like a drop in Conficker prevalence, this figure is affected by the changes in naming and statistical measurement mentioned earlier: there’s no indication of a significant drop in Conficker infections covering all variants.
5. JS/Iframe
Previous Ranking: 4
Percentage Detected: 2.85%
JS/Iframe.AS is a trojan that redirects the browser to a specific URL location with malicious software. The program code of the malware is usually embedded in HTML pages.
6. Win32/Sirefef
Previous Ranking: 6
Percentage Detected: 2.66%
Win32/Sirefef.A is a trojan that redirects results of online search engines to web sites that contain adware.
7. Win32/Dorkbot
Previous Ranking: 9
Percentage Detected: 2.10%
Win32/Dorkbot.A is a worm that spreads via removable media. The worm contains a backdoor. It can be controlled remotely. The file is run-time compressed using UPX.
The worm collects login user names and passwords when the user browses certain web sites. Then, it attempts to send gathered information to a remote machine. This kind of worm can be controlled remotely.
8. Win32/Sality
Previous Ranking: 12
Percentage Detected: 1.89%
Sality is a polymorphic file infector. When run starts a service and create/delete registry keys related with security activities in the system and to ensure the start of malicious process each reboot of operating system.
It modifies EXE and SCR files and disables services and process related to security solutions.
More information relating to a specific signature:
http://www.eset.eu/encyclopaedia/sality_nar_virus__sality_aa_sality_am_sality_ah
9. JS/TrojanDownloader.Iframe.NKE
Previous Ranking: 7
Percentage Detected: 1.78%
It is a trojan that redirects the browser to a specific URL location with malicious software. The program code of the malware is usually embedded in HTML pages.
10. Win32/Ramnit
Previous Ranking: 13
Percentage Detected: 1.21%
It is a file infector. It’s a virus that executes on every system start.It infects dll and exe files and also searches htm and html files to write malicious instruction in them. It exploits vulnerability on the system (CVE-2010-2568) that allows it to execute arbitrary code. It can be controlled remotley to capture screenshots, send gathered information, download files from a remote computer and/or the Internet, run executable files or shut down/restart the computer.
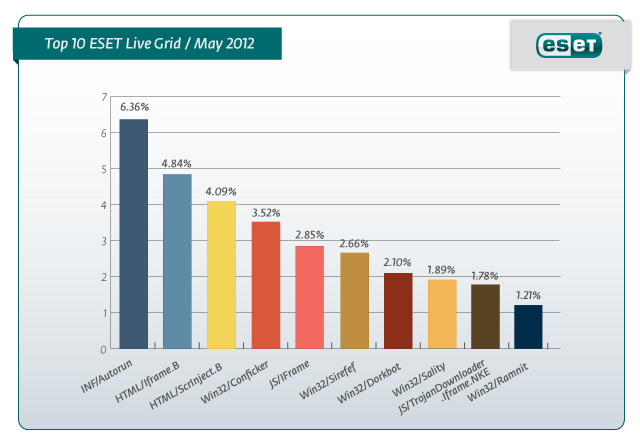
May Threats: INF/Autorun Returns to Top Spot
Throughout May, HTML/ScrInject.B was dethroned as top malware worldwide and Europe making the way for the big comeback of INF/Autorun – with a 6.36% infection rate globally and 4.99% in Europe. ESET malware statistics based on ESET Live Grid® – a cloud-based malware collection system utilizing data from users of ESET solutions worldwide has put HTML/Iframe.B in second spot, both in the world (4.84%) and in Europe (4.81%). HTML/ScrInject.B was recorded in third position with 4.09% infection rate worldwide and 4.35% in Europe.
INF/Autorun stands for a variety of malware using the file autorun.inf as a way of compromising a PC. This file contains information on programs meant to run automatically when removable media (often USB flash drives) are accessed by a Windows PC user. HTML/Iframe.B denotes a generic detection of malicious IFRAME tags embedded in HTML pages, which redirect the browser to a specific URL location containing malicious software. HTML/ScrInject.B is a generic detection of HTML web pages containing an obfuscated script or iframe tag that automatically redirects the user to the malware download.
Flame/Flamer or Win32/Flamer.A. as ESET refers to this very complex form of malware has been an interesting piece of malware intercepted by our malware research lab. “About the only good news is that Flamer, the latest piece of state-sponsored digital terrorism to come to light, is not likely to be headed your way any time soon. It is unlikely that you are the target of Flamer unless you are an official in a Middle Eastern government or working on weapons research for such a government,” says ESET‘s Security Evangelist Stephen Cobb. Flamer is not “out there” on the Internet right now, spreading from country to country. Users are not likely to find Flamer attached to an email in your Outlook Inbox (USB flash drives seem to be Flamer’s infection vector of choice). And if they are using a good antivirus product, it is now protecting you from Flamer. All the major AV products were quickly updated to detect Flamer and the better ones will now have generic detection of this malware that operates on “Flamer-like” characteristics.
“Perhaps more important, and this needs to be stressed, organizations that follow information security best practices, such as deploying endpoint security with device controls to prevent malware infection spreading viaUSB flash drives, are well-defended against most of the malicious software attacks they are likely to encounter today,” adds Cobb, based out of ESET’s North American center in San Diego. In one recent study, it was found that over 90 percent of security breaches could have been prevented with simple, cheap, or intermediate measures. This is good news for companies and consumers that are striving to align themselves with security best practices to defend againstmalware.
For more on the Flamer threat go to Stephen Cobb’s blogpost “Stuxnet, Flamer, Flame, Whatever Name: There’s No Good Malware” on ESET.com.
About ESET Live Grid®
ESET Live Grid® is ESET’s cloud-based malware collection system utilizing data from users of ESET solutions worldwide. This continual streaming of information provides ESET Malware Lab specialists with real-time accurate snapshot of the nature and scope of global infiltrations. Careful analysis of the threats, attack vectors and patterns serves ESET to fine-tune all heuristic and signature updates ̶ to protect its users against tomorrow’s threats.

One thought on “Monthly Threat Report: May 2012”