Survey Reveals Chasm between Users’ Concerns and Behaviour
A recent Survey commissioned by ESET and conducted online by Harris Interactive from May 31-June 2, 2011 among 2,027 U.S. adults 18+ found a startling disconnect between user concerns about privacy and security and their actions on social networking sites.
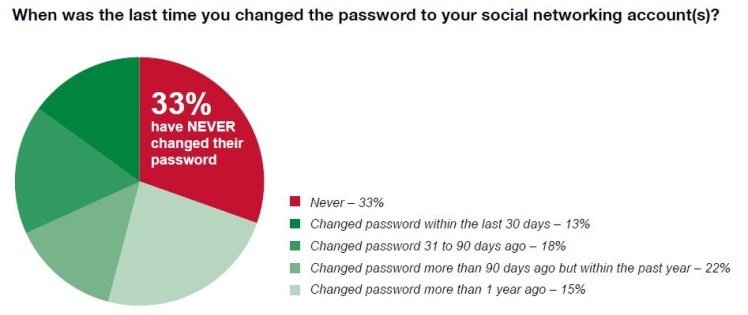
The study found that 69% of online social networking account owners are concerned about security on social networking sites, yet 1/3 of them have never changed their passwords for their social networking accounts and another 15% last changed their password more than one year ago.
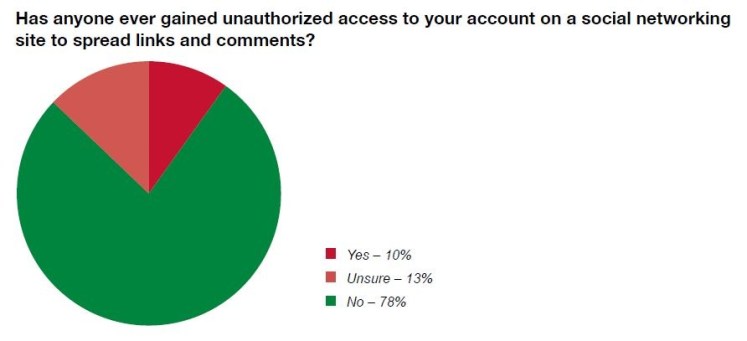
Moreover, the survey revealed that one in ten online Americans with social networking accounts have reported that an unknown party gained unauthorised access to their social networking account to spread malicious links and comments. This is particularly alarming since unauthorized access can threaten account owner’s cybersecurity as well as that of their contacts—we’ve seen countless examples, including recent scams around the death of Osama Bin Laden.
The survey also found that 67% of account owners claimed that they were concerned about privacy issues, yet 55% of the account owners update their privacy settings less often than once every six months, if ever. This can be problematic. For example, Facebook makes it extremely difficult to know when you need to change settings because they virtually never advise users when they are making changes that may affect user privacy.
While 69% of account owners were concerned about security and 67% expressed concern about privacy there were other significant concerns reported as well.
- 37% of were concerned about someone creating a fake account in their name.
- 95% of social networking account owners accept friend/follower/connection request always or sometimes.
- 71% of social networking account owners are concerned that their personal information entered on social networking sites may be sold or shared without their knowledge for profit.
- 17% were concerned about their children using social networking sites.
What can you do to secure yourself and your contacts on social networks?
A common misperception seems to have many users believing that social networking safety and privacy is entirely outside of their control. This is not the case—you can easily improve your online security if you follow these simple guidelines:
1. Use strong passwords
2. Know your options when it comes to privacy, and check back often.
3. Know who your real “friends” are.
When in doubt, seek help from outside resources.
Methodology
This survey was conducted online within the United States by Harris Interactive on behalf of Schwartz Communications from May 31-June 2, 2011 among 2,027 adults ages 18 and older, of whom 1,476 have social networking accounts. This online survey is not based on a probability sample and therefore no estimate of theoretical sampling error can be calculated.
Ireland: Password Security Improving
Urban Schrott, IT Security & Cybercrime Analyst, ESET Ireland
While hacking and data leakages are filling the headlines worldwide, we’ve looked at a more immediate aspect of personal security – passwords. Because hacking must invest at least a minimum of effort to get somewhere, it is an everlasting mystery why the vast majority of computer users would make the job so much easier for hackers by using the simplest and easiest to guess passwords. According to sources, globally the most widespread passwords are still “123456″ and “password” as well as other very simple ones.
This seemed just too terrible to us, so at ESET Ireland we had a survey carried out among Irish computer users, to see if they are any smarter than that. Well, we’re happy to say, yes they are! At least, a bit smarter. The survey was conducted to find out what sort of passwords the Irish use and how secure they are. We asked Irish computer users if their passwords resemble those in the several groups we made available, which reflect different levels of complexity and therefore increasing levels of protection.
Research was carried out by Amárach on behalf of ESET Ireland. In order to make a valid survey, a varied target audience, totalling 1000, was used. An 850 sample was derived online and a 150 sample was conducted face to face to ensure a fully representative sample.
The question we asked was “What does your email password look like?” and the optional answers given to the target audience were:
- I use a combination of letters and numbers (examples: jimmy34, ron45xyz, ilrw12)
- I use a simple word or sequence as password (examples: password, colin, 13435)
- I use a fictitious word as password (examples: lianwer, gianron, cavoveti)
- I use a lowercase and capital letters and numbers (examples: Roisin 75, OpeRal1982)
- I use a lowercase and capital letters, punctuation marks and numbers combined (examples: MoCon-07, McBett0982!)
- I use longer expressions (examples: Don’tforgettocallmother, Ican’tbebeaten)
- I don’t know my password for my main email account, because the computer stores it
The results we got are shown in the chart: https://blog.eset.ie/wp-content/uploads/2011/06/eset_ie_survey_11.jpg
While the situation is not optimal in that we’d prefer to see the majority using complex passwords (according to the survey, only about 10% do), it is still a step in the right direction in that:
- 38% are using a combination of letters and numbers for their passwords.
- 10% are using complex passwords.
- 10% more are using letters numbers and capitalization
That tells us that 58% of our respondents are in the category of users that don’t use the simplest “12345” passwords. So the constant attempts by ESET and others to raise awareness must have paid off, at least to a certain extent.
In a series of articles, David Harley has also been dealing with the issue of password security, but one worth pointing out in light of recent hacking events is the thought that “the best password in the world is of little use if the site or service or organization that you access with it isn’t taking proper care of it“, from the Password Strategies: Who Goes There article in SC Magazine.
So, while we do have a fantastically detailed and comprehensive White paper by David Harley and Randy Abrams available on Good Password Practice, and we do have the Irish example of computer users starting to take good practices to heart, further effort must be put into ensuring that service providers understand the importance of data protection and take adequate measures to ensure that confidential data stay confidential.
CTAC tile (staying in touch with ESET research)
Recently, we summarized on the ESET ThreatBlog a number of ways in which you can stay in touch with CTAC (the Cyber Threat Analysis Center). The ESET blog page is at http://blog.eset.com/ and has an RSS feed. Randy Abrams and David Harley write several articles a week for SC Magazine’s Cybercrime Corner. The ESET white papers page includes (among others) sections for:
- ESET conference papers
- Articles by or featuring ESET researchers
- ESET white papers
- ESET presentations
The latest additions to the white papers page are presentations by David Harley (in PDF format, but including speaker notes) from Infosecurity UK 2011 (Infrastructure Attacks: The Next Generation?) and EICAR 2011 (Security Software and Rogue Economics: The Presentation) – the EICAR conference paper is itself available here.
A number of Twitter accounts are used to flag ESET output:
@ESETresearch, @ESETLLC, @ESET_CTAC, and @dharleyatESET are directly linked to CTAC.
@esetkb retweets Knowledgebase articles and videos, and @ESET sometimes flags CTAC output.
There is also a CTAC Facebook page, an ESET USA Facebook page at http://www.facebook.com/esetusa, and an ESET global page http://www.facebook.com/esetsoftware. There are lots of regional ESET FB pages, too: too many to list here.
Also, you can find ESET Latin America’s research team (contents in Spanish language), on their blog (http://blogs.eset-la.com/laboratorio) or Twitter account (@esetla).
INF/Autorun: Threat Losing Thread?
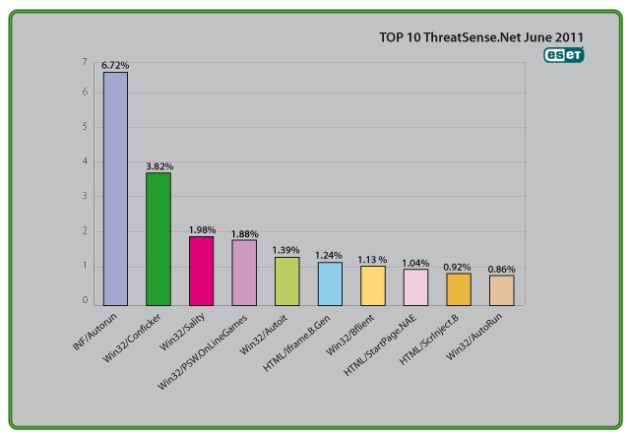
Microsoft issued a blog this month about its success in slashing the volume of malware infections exploiting the Autorun facility: INF/Autorun is ESET’s generic detection covering a wide range of malware families that install or modify autorun.inf files in order to infect systems. We’ve been explaining for a long time why Autorun has presented such a problem in recent years – see the text relating to INF/Autorun in the Top Ten section below – and consistently appearing in the Top three in ESET’s ThreatSense.Net® monthly figures.
In recent years, Microsoft has taken steps to address this loophole: firstly by turning off Autorun by default in Windows 7, then by making patches available for XP, Vista and Windows Server, and finally by pushing the changes out through Windows Update so that many more systems would then be updated automatically. Better late than never, some would say: in fact, ESET’s Director of Technical Education Randy Abrams has described it as “a very late response to a well-known problem that had a very predictable response”.
However, if you regularly read these reports, you’ll notice something a little strange. The dramatic drop in Microsoft’s report isn’t reflected in the ThreatSense.Net® figures. Fundamentally, that’s because we aren’t measuring the same things: Microsoft tells us that it saw infections on XP and Vista reduced by 1.3 million between February and May, but the telemetry we use for these reports isn’t measuring infections, but detections. As Randy puts it, “We are tracking shots on goal where Microsoft is tracking goals.” Actually, the first chart in the Microsoft blog is doing the same thing, so Chart 1 and Chart 2 are actually not directly comparable even there. In fact, when ESET Distinguished Researcher Aryeh Goretsky used similar metrics, he observed a similar, generally downward trend to that reported by Microsoft.
There are other factors, too. While there’s obviously an overlap between Microsoft’s customer-base and ours (an awful lot of ESET customers are running Windows!), we’re obviously not monitoring identical populations. Consider, for instance, the fact that XP SP2 is out of support, so that the figures for machines that aren’t updated beyond that show only a small drop. But that doesn’t, of course, mean that they aren’t a channel for infection attempts. And while a generic detection like INF/Autorun is optimal from the end-user’s point of view because it catches a wide range of malware in high volumes, it’s not so well-suited for accurate categorization of individual threats and threat families: that would be a gargantuan task, and not actually very useful to the customer.
As for looking at infections versus infected machines, neither approach is “wrong”: they just look at the threatscape from different perspectives.
Support Scams Not Gone, Not Forgotten
David Harley, ESET Senior Research Fellow
It has been blogged a great deal in the last year or two the type of support scam where someone calls you out of the blue (“cold-calling”) to “help you” with a malware problem you didn’t know you had, or to help you check your system for problems – but the issue seems to have come to life in the media again following a survey by Microsoft enquiring into this “emerging” threat. Emerging doesn’t seem quite the right word for a threat that’s been around for well over a year, but the survey came up with some interesting if disquieting figures, as it has been discussed in a recent blog.
It’s assumed in the Microsoft press release that if someone calls you out of the blue to tell you that you have a computer problem, it’s going to be a scam. Well, that’s probably generally true in the countries mentioned, but it’s actually more complicated than that. As we explained here, there are circumstances in which you might be cold-called legitimately in certain countries and in certain contexts. And in a white paper, we’ve tried to address some of the legal issues as well as providing a comprehensive picture of how the scams tend to work.
The press release contains some good advice but it didn’t mention a couple of things:
- Most (though not all) of these scams rely on persuading you to run Event Viewer, which is pretty useless as a diagnostic tool unless you already know enough about Windows internals not to fall for the scam. It flags a whole bunch of transient errors that may frighten a technically-challenged victim, but don’t actually signify a real problem at all, so if someone tries to get you to run a program called EVENTVWR, that’s a pretty good scam heuristic in itself.
- While the survey didn’t include Australia, that’s also a very commonly targeted population: CNET is incorrect (http://news.cnet.com/8301-1009_3-20071568-83/scammers-turning-to-phone-calls-to-gain-pc-access/ ) in saying that only the countries surveyed are seeing the problem at the moment. It’s true, of course, that other countries with a large English-speaking population could be targeted, and that the scammers might start targeting speakers of other languages.
The Top Ten Threats
1. INF/Autorun
Previous Ranking: 1
Percentage Detected: 6.72%
This detection label is used to describe a variety of malware using the file autorun.inf as a way of compromising a PC. This file contains information on programs meant to run automatically when removable media (often USB flash drives and similar devices) are accessed by a Windows PC user. ESET security software heuristically identifies malware that installs or modifies autorun.inf files as INF/Autorun unless it is identified as a member of a specific malware family.
Removable devices are useful and very popular: of course, malware authors are well aware of this, as INF/Autorun’s frequent return to the number one spot clearly indicates. Here’s why it’s a problem.
The default Autorun setting in Windows will automatically run a program listed in the autorun.inf file when you access many kinds of removable media. There are many types of malware that copy themselves to removable storage devices: while this isn’t always the program’s primary distribution mechanism, malware authors are always ready to build in a little extra “value” by including an additional infection technique.
While using this mechanism can make it easy to spot for a scanner that uses this heuristic, it’s better, as Randy Abrams has suggested in our blog (http://www.eset.com/threat-center/blog/?p=94; http://www.eset.com/threat-center/blog/?p=828) to disable the Autorun function by default, rather than to rely on antivirus to detect it in every case. You may find Randy’s blog at http://www.eset.com/threat-center/blog/2009/08/25/now-you-can-fix-autorun useful, too.
2. Win32/Conficker
Previous Ranking: 2
Percentage Detected: 3.82%
The Win32/Conficker threat is a network worm originally propagated by exploiting a recent vulnerability in the Windows operating system. This vulnerability is present in the RPC sub-system and can be remotely exploited by an attacker without valid user credentials. Depending on the variant, it may also spread via unsecured shared folders and by removable media, making use of the Autorun facility enabled at present by default in Windows (though not in Windows 7).
Win32/Conficker loads a DLL through the svchost process. This threat contacts web servers with pre-computed domain names to download additional malicious components. Fuller descriptions of Conficker variants are available at http://www.eset.eu/buxus/generate_page.php?page_id=279&lng=en.
While ESET has effective detection for Conficker, it’s important for end users to ensure that their systems are updated with the Microsoft patch, which has been available since the third quarter of 2008, so as to avoid other threats using the same vulnerability. Information on the vulnerability itself is available at http://www.microsoft.com/technet/security/Bulletin/ms08-067.mspx. While later variants dropped the code for infecting via Autorun, it can’t hurt to disable it: this will reduce the impact of the many threats we detect as INF/Autorun. The Research team in San Diego has blogged extensively on Conficker issues: http://www.eset.com/threat-center/blog/?cat=145
It’s important to note that it’s possible to avoid most Conficker infection risks generically, by practicing “safe hex”: keep up-to-date with system patches, disable Autorun, and don’t use unsecured shared folders. In view of all the publicity Conficker has received and its extensive use of a vulnerability that’s been remediable for so many months, we’d expect Conficker infections to be in decline by now if people were taking these commonsense precautions. While the current ranking looks like a drop in Conficker prevalence, this figure is affected by the changes in naming and statistical measurement mentioned earlier: there’s no indication of a significant drop in Conficker infections covering all variants.
3. Win32/Sality
Previous Ranking: 4
Percentage Detected: 1.98%
Sality is a polymorphic file infector. When run starts a service and create/delete registry keys related with security activities in the system and to ensure the start of malicious process each reboot of operating system.
It modifies EXE and SCR files and disables services and process related to security solutions.
More information relating to a specific signature:
http://www.eset.eu/encyclopaedia/sality_nar_virus__sality_aa_sality_am_sality_ah
4. Win32/PSW.OnLineGames
Previous Ranking: 3
Percentage Detected: 1.88%
This is a family of Trojans used in phishing attacks aimed specifically at game-players: this type of Trojan comes with keylogging and (sometimes) rootkit capabilities which gather information relating to online games and credentials for participating. Characteristically, the information is sent to a remote intruder’s PC.
These Trojans are still found in very high volumes, and game players need to remain alert. While there have always been unpleasant people who will steal another gamer’s credentials just for the heck of it, trading in virtual cash, treasure, avatars and so on is now a major source of illegal income for cybercriminals. It’s also important that participants in MMORPGs (Massively Multi-player Online Role Playing Games) like Lineage and World of Warcraft, as well as “metaverses” like Second Life, continue to be aware of the range of other threats like griefing ranged against them. The ESET Research team considered gaming malware in detail in the ESET 2008 Year End Global Threat Report, which can be found at http://www.eset.com/threat-center/threat_trends/EsetGlobalThreatReport(Jan2009).pdf
5. Win32/Autoit
Previous Ranking: 8
Percentage Detected: 1.39%
Win32/Autoit is a worm that spreads via removable media, and some of it variants spread also thru MSN. It may arrive on a system as a downloaded file from a malicious Web site. It may also be dropped by another malware. After infecting a system, it searches for all the executable files and replace them with a copy of itself. It copies to local disks and network resources. Once executed it downloads additional threats or variants of itself.
In order to ensure that the worm is launched automatically when the system is rebooted, the worm adds a link to its executable file to the system registry.
6. HTML/Iframe.B.Gen
Previous Ranking: 7
Percentage Detected: 1.24%
Type of infiltration: Virus
HTML/Iframe.B.Gen is generic detection of malicious IFRAME tags embedded in HTML pages, which redirect the browser to a specific URL location with malicious software.
7. Win32/Bflient
Previous Ranking: 9
Percentage Detected: 1.13%
Win32/Bflient is a worm that spreads via removable media and contains a backdoor. It can be controlled remotely and ensures it is started each time infected media is inserted into the computer.
8. HTML/StartPage.NAE
Previous Ranking: 5
Percentage Detected: 1.04%
HTML/StartPage.NAE is a trojan which tries to promote certain web sites by modifying the window’s registry. The program code of the malware is usually embedded in HTML pages. The aim of this malware is to change the website that is first opened when running Microsoft Internet Explorer (only affected browser). This way it promotes a specific website, and the owner of it profits of the increasing amount of visitors. This specific variant of HTML/StartPage redirects the affected users to the following website: hxxp://duzceligenclik.com
9. HTML/ScrInject.B
Previous Ranking: 11
Percentage Detected: 0.92%
Generic detection of HTML web pages containing script obfuscated or iframe tags that that automatically redirect to the malware download.
10. Win32/AutoRun
Previous Ranking: 10
Percentage Detected: 0.86%
Threats identified with the label ‘AutoRun’ are known to use the Autorun.INF file. This file is used to automatically start programs upon insertion of a removable drive in a computer. The file itself doesn´t represent a threat, but combined with a binary file it turns into a deploying feature.