Facebook privacy: security concerns
If Facebook was a country, it would be the third largest one in the world (http://blog.eset.com/2011/05/04/osama-bin-laden-is-alive-and-well-on-facebook). All those Facebook users are exposed to the many social networking risks and nuisances that are regularly reported nowadays. Paul Laudanski’s wrote a comprehensive blog article which is a timely and essential guide to a better and safer management of a Facebook account.
As Paul points out, breaches can and do occur, and the only way to truly protect the information is to not have it online. However, that would be a sort of defeat to the purpose of social networking. The best thing to do is to understand the risks and take all reasonable measures to protect oneself against scams and identity theft.
Cybersecurity symposium in San Diego
Securing Our eCity (SOeC ), originated in the city of San Diego, California (USA), has celebrated a new event that brought together various people connected with this interesting cyber security education initiative, which for more than two years it has been expanding.
On May 17th, all day, over a hundred people attended to the first of two annual symposiums organized by SOeC. ESET was there to attend conferences of various specialists in education, technology and cyber security sectors including governments, businesses and nonprofit organizations.
The presentations were all related to the initiative, such as the problems raise public awareness on cyber security, the same approach I business and the role of governments around the theme. Among the featured speakers were: Ernest McDuffie, leader of the national education initiative of the prestigious cyber security NIST (National Institute of Standards and Technologies), Ruben Barrales, CEO of the Chamber of Commerce San Diego Regional, Nathan Fletcher, California legislature, Darin Andersen, Chief Operating Officer (COO) of ESET North America and Duane Roth, CEO of Connect, an organization dedicated to supporting entrepreneurs.
The symposium featured three panels of experts: one focused on the problem especially in small and medium enterprises, the other on the laws and regulations relating to the business, and one on the need to prepare leaders who have the ability to handle the issue the future.
There were also two workshops, one of which was security at the household level, and the other on the resources required to create a framework in information security within an organization. The event ended with an awards ceremony and delivery of annual awards to executives in information technology.
Return of the password reset attack
Randy Abrams, director of technical education, ESET
Most people know about the Sony PlayStation Network/Qriocity Service breach by now. Probably most of those people know that they need to change those account passwords when they can access the network again. Many people might be aware that if they used the same password in other places, they need to change those passwords as well. Sony doesn’t seem to know if credit card details were breached, so many people are cancelling the credit cards used in conjunction with their Sony accounts.
The insidious threat that many people may miss is the compromise of the answers to password reset questions. That was some of the data that was reportedly compromised in the breach, and has perpetual consequences if you do not change your security reset answers on other sites as well.
The way the password reset attack works is that a hacker tries to log into your account. It may be an email account, a social networking account, a blogging account, or another type of online account. The hacker clicks the link for “I forgot my password” and is challenged with security questions. Having obtained the answers from the Sony data breach, the hacker knows the answers to the reset questions and is now able to commandeer your accounts, depending on the mechanism that particular sites use in conjunction with the security challenge questions.
If you are one of the victims of the Sony breach, do not overlook the significance of the challenge questions. You need to determine each site you are signed up with, and if they use any of the same security challenge questions that were used on the Sony site. Failure to change the answers may leave your other accounts vulnerable to cybercriminals performing password reset attacks.
The Top Ten Threats
1. INF/Autorun
Previous Ranking: 1
Percentage Detected: 6.58%
This detection label is used to describe a variety of malware using the file autorun.inf as a way of compromising a PC. This file contains information on programs meant to run automatically when removable media (often USB flash drives and similar devices) are accessed by a Windows PC user. ESET security software heuristically identifies malware that installs or modifies autorun.inf files as INF/Autorun unless it is identified as a member of a specific malware family.
Removable devices are useful and very popular: of course, malware authors are well aware of this, as INF/Autorun’s frequent return to the number one spot clearly indicates. Here’s why it’s a problem.
The default Autorun setting in Windows will automatically run a program listed in the autorun.inf file when you access many kinds of removable media. There are many types of malware that copy themselves to removable storage devices: while this isn’t always the program’s primary distribution mechanism, malware authors are always ready to build in a little extra “value” by including an additional infection technique.
While using this mechanism can make it easy to spot for a scanner that uses this heuristic, it’s better to disable the Autorun function by default, rather than to rely on antivirus to detect it in every case.
2. Win32/Conficker
Previous Ranking: 2
Percentage Detected: 3.61%
The Win32/Conficker threat is a network worm originally propagated by exploiting a recent vulnerability in the Windows operating system. This vulnerability is present in the RPC sub-system and can be remotely exploited by an attacker without valid user credentials. Depending on the variant, it may also spread via unsecured shared folders and by removable media, making use of the Autorun facility enabled at present by default in Windows (though not in Windows 7).
Win32/Conficker loads a DLL through the svchost process. This threat contacts web servers with pre-computed domain names to download additional malicious components. Fuller descriptions of Conficker variants are available at http://www.eset.eu/buxus/generate_page.php?page_id=279&lng=en.
While ESET has effective detection for Conficker, it’s important for end users to ensure that their systems are updated with the Microsoft patch, which has been available since the third quarter of 2008, so as to avoid other threats using the same vulnerability. Information on the vulnerability itself is available at http://www.microsoft.com/technet/security/Bulletin/ms08-067.mspx. While later variants dropped the code for infecting via Autorun, it can’t hurt to disable it: this will reduce the impact of the many threats we detect as INF/Autorun.
It’s important to note that it’s possible to avoid most Conficker infection risks generically, by practicing “safe hex”: keep up-to-date with system patches, disable Autorun, and don’t use unsecured shared folders. In view of all the publicity Conficker has received and its extensive use of a vulnerability that’s been remediable for so many months, we’d expect Conficker infections to be in decline by now if people were taking these commonsense precautions. While the current ranking looks like a drop in Conficker prevalence, this figure is affected by the changes in naming and statistical measurement mentioned earlier: there’s no indication of a significant drop in Conficker infections covering all variants.
3. Win32/PSW.OnLineGames
Previous Ranking: 3
Percentage Detected: 1.92%
This is a family of Trojans used in phishing attacks aimed specifically at game-players: this type of Trojan comes with keylogging and (sometimes) rootkit capabilities which gather information relating to online games and credentials for participating. Characteristically, the information is sent to a remote intruder’s PC.
These Trojans are still found in very high volumes, and game players need to remain alert. While there have always been unpleasant people who will steal another gamer’s credentials just for the heck of it, trading in virtual cash, treasure, avatars and so on is now a major source of illegal income for cybercriminals. It’s also important that participants in MMORPGs (Massively Multi-player Online Role Playing Games) like Lineage and World of Warcraft, as well as “metaverses” like Second Life, continue to be aware of the range of other threats like griefing ranged against them. The ESET Research team considered gaming malware in detail in the ESET 2008 Year End Global Threat Report, which can be found at http://www.eset.com/threat-center/threat_trends/EsetGlobalThreatReport(Jan2009).pdf
4. Win32/Sality
Previous Ranking: 4
Percentage Detected: 1.88%
Sality is a polymorphic file infector. When run starts a service and create/delete registry keys related with security activities in the system and to ensure the start of malicious process each reboot of operating system.
It modifies EXE and SCR files and disables services and process related to security solutions.
More information relating to a specific signature:
http://www.eset.eu/encyclopaedia/sality_nar_virus__sality_aa_sality_am_sality_ah
5. HTML/StartPage.NAE
Previous Ranking: 17
Percentage Detected: 1.78%
HTML/StartPage.NAE is a trojan which tries to promote certain web sites by modifying the window’s registry. The program code of the malware is usually embedded in HTML pages. The aim of this malware is to change the website that is first opened when running Microsoft Internet Explorer (only affected browser). This way it promotes a specific website, and the owner of it profits of the increasing amount of visitors. This specific variant of HTML/StartPage redirects the affected users to the following website: hxxp://duzceligenclik.com
6. JS/Redirector
Previous Ranking: 11
Percentage Detected: 1.59%
JS/Redirector.NID is a trojan that redirects the browser to a specific URL location with malicious software. The program code of the malware is usually embedded in HTML pages of compromised legit websites. As indicated by its name, it uses a JavaScript, usually obfuscated, to make the redirection to the malicious website. By doing this, it tries to download and execute malicious software on the clients computer, a distribution technique widely used.
7. HTML/Iframe.B.Gen
Previous Ranking: 7
Percentage Detected: 1.59%
Type of infiltration: Virus
HTML/Iframe.B.Gen is generic detection of malicious IFRAME tags embedded in HTML pages, which redirect the browser to a specific URL location with malicious software.
8. Win32/Autoit
Previous Ranking: 5
Percentage Detected: 1.28%
Win32/Autoit is a worm that spreads via removable media, and some of it variants spread also thru MSN. It may arrive on a system as a downloaded file from a malicious Web site. It may also be dropped by another malware. After infecting a system, it searches for all the executable files and replace them with a copy of itself. It copies to local disks and network resources. Once executed it downloads additional threats or variants of itself.
In order to ensure that the worm is launched automatically when the system is rebooted, the worm adds a link to its executable file to the system registry.
9. Win32/Bflient
Previous Ranking: 8
Percentage Detected: 0.85%
Win32/Bflient is a worm that spreads via removable media and contains a backdoor. It can be controlled remotely and ensures it is started each time infected media is inserted into the computer.
10. Win32/Autorun
Previous Ranking: 6
Percentage Detected: 0.96%
Threats identified with the label ‘AutoRun’ are known to use the Autorun.INF file. This file is used to automatically start programs upon insertion of a removable drive in a computer. The file itself doesn´t represent a threat, but combined with a binary file it turns into a deploying feature.
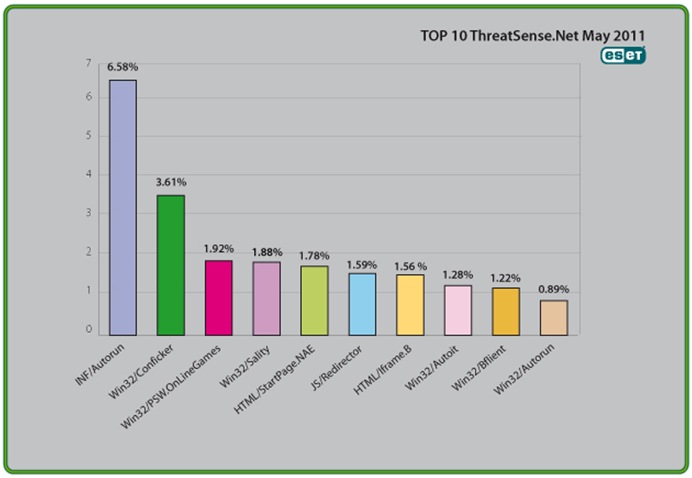
Top Ten Threats at a Glance (graph)
Analysis of ESET’s ThreatSense.Net®, a sophisticated malware reporting and tracking system, shows that the highest number of detections this month, with almost 6.58% of the total, was scored by the INF/Autorun class of threat.

Reference your post about INF/autorun threat. I could not access any further information.
When I clicked on the Blog address given in your email the following message appeared:-
ESET
404 error. We are sorry, the page you requested cannot be found.
Not much help to me then!
Hi James,
Thank you for the info.
That link was meant to be on eset.com page over which we have no control. Removed it now.
Thanks Urban. No problem! I have every confidence in Eset’s ability to provide maximum protection. Nevertheless I scrutinise everything that pops up on my screen. If there is the slightest doubt I reach for the delete button. Meantime keep on chasing those “baddies.”
Regards, Jim.