Beyond TeslaCrypt: Crysis, a new ransomware family lays claim to parts of its territory
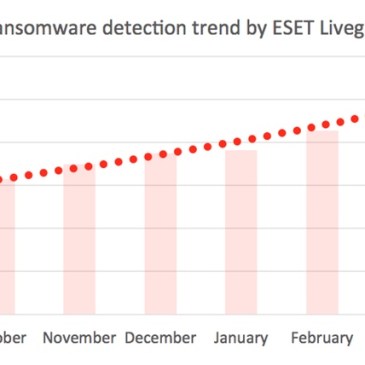
It has been two weeks since ESET created a TeslaCrypt decryptor, which allows victims of the ransomware to get their files back. This came on the back of its developers ceasing operations. Since then, over 32,000 users around the globe have taken advantage of this opportunity and downloaded the tool. But even with TeslaCrypt abandoning its territory, … More Beyond TeslaCrypt: Crysis, a new ransomware family lays claim to parts of its territory